 Continent 8 (C8) has recently added 5 new co-location sites to its US footprint in addition to existing sites in-state (live overall in 29 US states and growing). C8 connects all of these sites to its global MPLS backbone and blended local and international internet peering, deploying regulated or community public cloud and backup.
Continent 8 (C8) has recently added 5 new co-location sites to its US footprint in addition to existing sites in-state (live overall in 29 US states and growing). C8 connects all of these sites to its global MPLS backbone and blended local and international internet peering, deploying regulated or community public cloud and backup.
In this article, Justin Cosnett, Chief Product Officer at Continent 8, will demonstrate how C8 is deploying these infrastructure assets as building blocks to enable a sportsbook or iGaming operator to deliver RESILIENCE and meet regulatory requirements for disaster recovery, business continuity and backup.
Why resilience?
It may seem obvious, but there are countless examples of where businesses have failed to implement resilience to secure business continuity by design from the outset, such as:
“getting live is the priority for our resources, we can sort resilience later”
“we can spend on resilience when we have achieved ROI for live”
“we use an N+1 infrastructure provider, we don’t need to add to that”
“the Internet is resilient by virtue of its distributed topology”
Therefore, it’s worth stating why resilience by design is in fact extremely important, especially for online operators in the gambling industry:
- It can be harder and more costly to add resilience later.
- When you are down, every minute is lost revenue, and possibly lost customers to competitors, causing permanent damage.
- Reputations with consumers, shareholders and partners are harder and more costly to recover after an incident.
- There is never a good time for a disaster, but it will always feel like “it happened at the worst time”.
- Regulators expect or require resilience, if you don’t have it when you need it, they will question other assumptions or confirmed capabilities in license application.
Resilience terminology
To get through the terminology quickly, and specifically for iGaming and sportsbook and the online technology utilised in the businesses, some resilient terminology:
- RTO and RPO – Recovery Time and Point Objective. Effectively the maximum amount of time any resilience design can allow (how long your business can be unavailable for, in minutes, hours, days since incident), and the maximum amount of data loss or point in time that can be recovered to (minutes, hours or days before incident). Active-Active implementations and incremental forever frequent backups can keep delivery very speedy or almost zero RTO and low RPO, but at significant cost.
- Business Impact Analysis (BIA) – The output of a review of financial, legal (regulatory) and possibly reputational outcomes of an event which stops the business being able to perform. This should be critical in aiding the case for both the justification (incl. budget) of any resilience strategy or even setting the RTO and RPO to be met.
- Backup – Point in time copies of data (to achieve RPO) or configurations stored ready for restoration as required to protect (transactional) data corruption, loss or be available for audit.
- Disaster Recovery – A process, plan, or method of recovering (usually technology infrastructure) service availability due to an unplanned and unexpected critical event (how to achieve RTO).
- Business Continuity – A method of ensuring (B2C or B2B online) service availability during or after a critical incident.
- Data Safe – Usually a regulated copy of transactional data used by regulators for audit purposes, and not usually a data set available for use as a backup.
For iGaming and sportsbook B2B or B2C operators, this applies to online “production” infrastructure to continue to service bet taking and completion. In this highly regulated environment, there can be infrastructure requirements which operators must adhere to in the specific jurisdiction in which they are operating.
NOTE: this can make physical segregation in distance difficult as the jurisdictions may be small or have limited options in smaller states, provinces, or countries.
Backup of data is usually a regulatory requirement as well as a component of a disaster recovery plan – irrespective of whether there is a regulated data safe component. Operators will be unlikely to be able to restore services or transaction history from a regulator operated data safe. Business Continuity may be assured through a resilient infrastructure architecture, or delivered via a disaster recovery plan, but may not meet the same regulatory backup requirement(s). Backups can often have two uses, for recovery in case of incident (RPO) and use for regulatory requirement (number of years to maintain data records).
Resilience by design
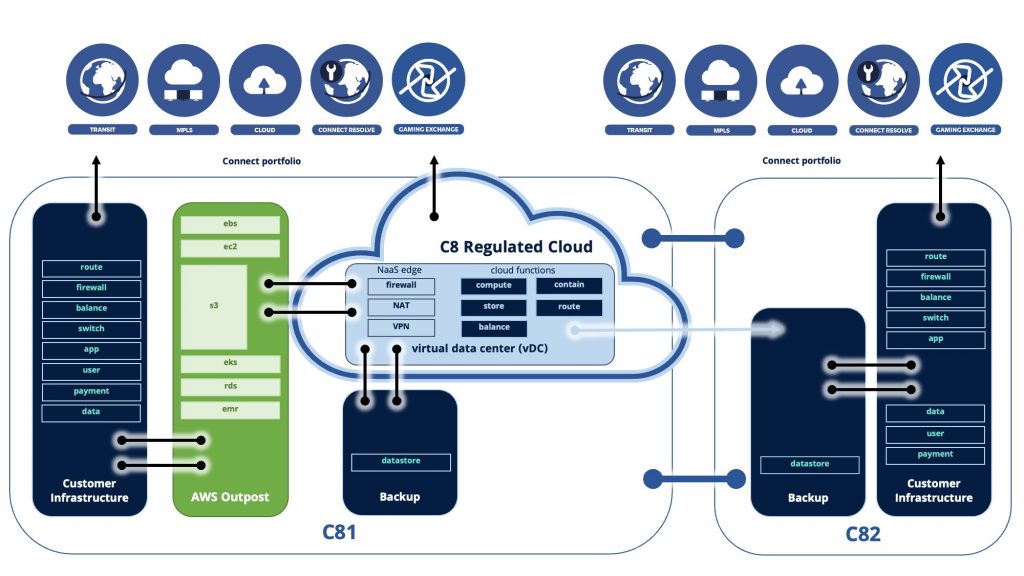
To maintain business continuity, a resilient infrastructure may be planned and executed which enables protection from single point of failure such as site loss, and this could be a dual hosted active-active implementation whereby customers are serviced live, and some sort of data integrity is ensured, usually at the database software level…
- BUT this may not protect against data corruption or cyber attack, so a disaster recovery plan may still be relevant, AS WELL AS secure backup
Similarly, great backup capability, even stored off-site with contracted fast retrieval, may meet regulatory requirements or protection against data corruption or cyber event…
- BUT if the data can’t be restored into an available or suitable regulatory infrastructure to deliver service, your business isn’t able to continue.
Other considerations – cyber?
With online businesses, especially iGaming, being targets for cyber attacks, disaster recovery and business continuity plans must consider prevention of the event as well as recovery in case of event.
From Ransomware to DDoS, to data exfiltration (or a combination), these can be business impacting events causing complete inability to continue. The use of encryption and backup corruption in an attack can hamper recovery capability or access to data, and are often deliberately targeting these areas to be successful.
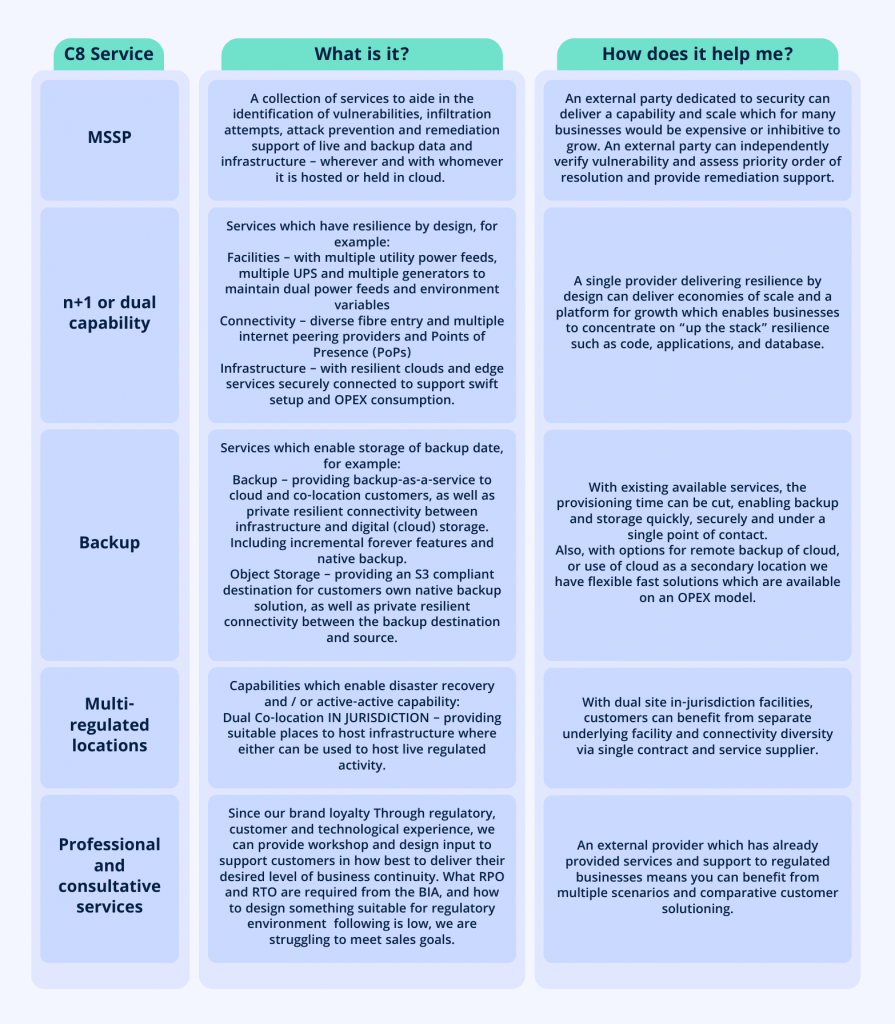
Prevention
Security services such as an MSOC (Managed Security Operations Center) inclusive SIEM (Security Incident and Event Management) platform, can help companies to benefit from expertise and scale to prevent, detect or remediate vulnerabilities and threats. These can be internal (unmanaged) resources dedicated to the business, usually in large enterprises, or managed as an outsourced delivery (Managed Security Services provider or MSSP). Via C8 Secure, Continent 8 offers these capabilities to our customers, along with private connectivity for data transport and access.
Recovery
Solid security and cyber protection of backup and secondary infrastructure is necessary to separate and limit an attacker’s ability to prevent recovery. Additionally, the use of MSOC, SIEM and backup technologies to scan backup data for potential vulnerabilities or infiltration.
How can we help?
We provide many of the building blocks or “as-a-service” capabilities necessary for operators and suppliers to create resilience and backup necessary, suitable to business requirements. There is no one size fits all, sometimes C8 is already providing a resilient service which can be consumed “as-is” and provides assurance, as surmised below.
Want to learn more about C8’s services? Get in touch via sales@continent8.com