
Why iGaming operators and sportsbooks should treat networking infrastructure as a revenue engine (not just infrastructure).
After a long four-year wait, the FIFA World Cup is back – and this one is a monster. FIFA World Cup 2026 will be the largest tournament ever, featuring 48 teams and 104 fixtures, running from 11 June to 19 July.
For sportsbooks and iGaming operators, that schedule isn’t just exciting – it’s a traffic forecast. World Cup season compresses peaks into tight windows: match starts, halftime surges, late goals, VAR drama, stoppage time, and knockouts. These moments produce short, intense betting spikes where latency, availability, and security directly affect conversion, player trust, and margins.
As a managed IT service provider focused on networking, specialising in the iGaming sector, here’s the core truth we see every time a global event hits:
Your platform doesn’t “run on the cloud.” It runs on the network path between the player and your service.
Over the last four years, networking has evolved from “pipes and ports” to a performance and security fabric spanning edge, cloud, and identity.
Why it matters for iGaming: these advances shift the goal from “keep the WAN up” to “optimise experience under load, under attack, and under regulatory constraints.”
From 2022 onward, the product playbook moved aggressively toward real-time, high-frequency engagement:
1) Live betting became the center of gravity
Operators doubled down on in-play experiences where odds update constantly, and settlement must be fast. That model demands low jitter, fast market data, predictable latency, and a trusted, secure iGaming infrastructure partner.
2) Microbetting and “fast markets” pushed latency requirements into the sub-second zone
Trade coverage of microbetting repeatedly highlights low latency as a foundational requirement – a small delay can misalign markets with real-world events and break trust.
3) A more complex ecosystem: more vendors, more APIs, more paths to fail
Modern sportsbooks are assembled from components (streaming/CDNs, risk engines, KYC/AML, payments, fraud, personalisation and sports data feeds). Each added dependency increases the need for network segmentation, resilient routing, and end-to-end observability.
Bottom line: Since 2022, sportsbooks have increasingly become real-time transaction platforms. And real-time platforms live or die on networking.

Remember Paul the Octopus, the 2010 World Cup “oracle” who predicted match outcomes by choosing between flag-labeled boxes? CNN documented how the method worked and how Paul became a phenomenon. Paul’s overall record is often summarised as 12 correct predictions out of 14 (~85.7%).
Will 2026 bring a new animal oracle? Maybe. But the only “oracle” sportsbooks should rely on is better: network telemetry (latency, loss, jitter, and availability) – because those predictions are actionable.
This is the uncomfortable part: the betting window is time-bound. If a user can’t place a bet when the moment happens, they don’t “come back later.” The moment is gone – and so is the revenue opportunity.
To ground that in real numbers, here’s a look at US sports betting performance over the last four years:
Real-world US sports betting stats (AGA)
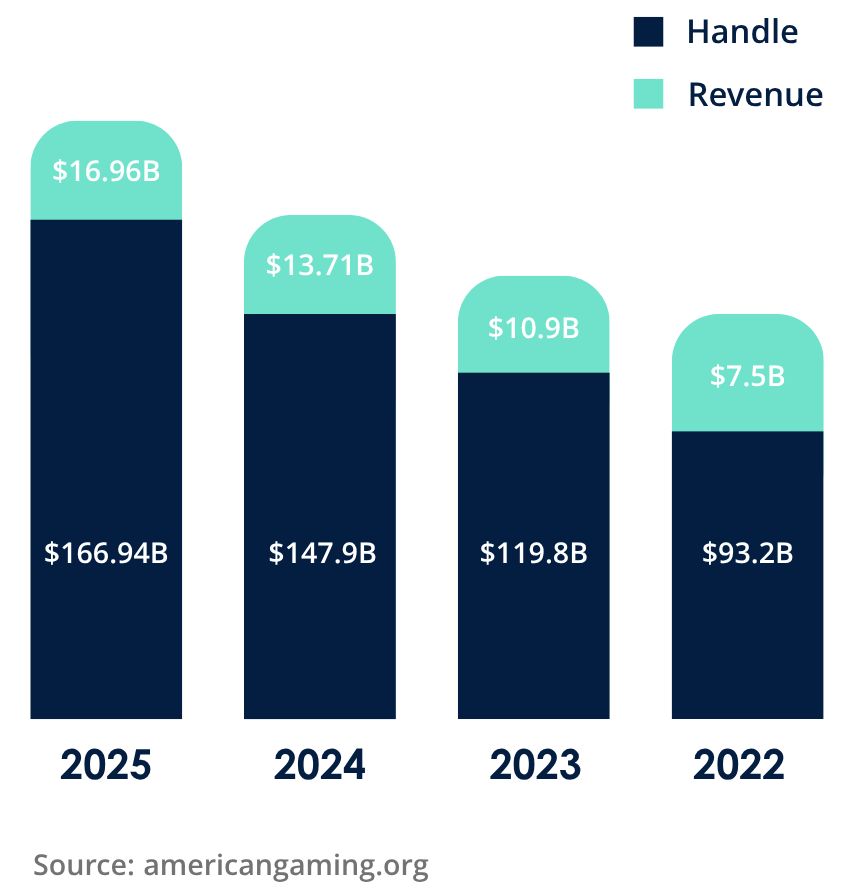
Now translate that into downtime risk:
In other words: downtime isn’t just an IT incident – it’s a commercial event.
If we had to summarise a World Cup networking plan in one sentence: Build for peak, defend for attack, and operate for recovery.
The 5 pillars we design around
World Cup 2026 will deliver 104 matches worth of demand shocks, and the operators who win won’t just have better odds or better promos – they’ll have better uptime, better latency, and better recovery.
The last four years prove why: US sports betting handle and revenue have climbed dramatically from 2022 through 2025.
As the market grows, the cost of downtime grows with it – and the network becomes the invisible line between “player excitement” and “player churn.” Are you ready to handle the traffic?
Continent 8 is a global iGaming network service provider, learn more about our trusted solutions here or contact the team via sales@continent8.com
Continent 8 Technologies, a leading provider of cutting‑edge managed IT solutions designed for the global iGaming and online sports betting industry, announces the launch of its comprehensive suite of AI-driven solutions. The portfolio is designed to help organisations harness the full potential of artificial intelligence across their operations and infrastructure, securely and in line with regulatory environments.
 The intelligence8 portfolio combines advanced infrastructure, intelligent automation, and managed services to enable operators and suppliers to deploy, scale, and optimise AI workloads with confidence. The suite currently includes four core offerings: AI-Ready Infrastructure, Managed AI Services, AI Ops, and Voice AI.
The intelligence8 portfolio combines advanced infrastructure, intelligent automation, and managed services to enable operators and suppliers to deploy, scale, and optimise AI workloads with confidence. The suite currently includes four core offerings: AI-Ready Infrastructure, Managed AI Services, AI Ops, and Voice AI.
Cris Kuehl, Chief Data, Information and AI Officer at Continent 8 Technologies, comments: “As AI adoption accelerates across industries, organisations face increasing challenges around performance, scalability, security, and operational complexity. Continent 8 addresses these challenges by delivering an integrated, enterprise-grade platform that simplifies AI deployment and management. With intelligence8, we are empowering our customers to move from AI ambition to real-world execution – while maintaining the strict standards required in regulated iGaming markets.”
The launch reinforces Continent 8’s commitment to delivering next-generation technology solutions that help customers stay competitive in a rapidly evolving digital landscape.
The suite is fully aligned with Continent 8’s global network of connected locations, offering customers secure, low-latency access to AI services in regulated iGaming jurisdictions globally and latency-sensitive environments worldwide.
Continent 8 will showcase the intelligence8 suite at SBC Summit Americas 2026, 9-11 June in Fort Lauderdale, Florida. Visit Booth 808 for a live demo or book a meeting in advance at: https://lp.continent8.com/sbc-summit-americas-2026
In a recent interview with G3 Magazine, Justin Cosnett, Chief Product Officer at Continent 8 Technologies, shared his insights on how major global sporting events are reshaping infrastructure demands across the betting industry.

The world’s biggest sporting events are no longer just moments-they are sustained digital stress tests for the global betting ecosystem.
Traditionally, operators prepared for short bursts of activity. A spike. A surge. A single, intense window.
But that model is rapidly becoming outdated.
The 2026 Super Bowl- and the upcoming FIFA World Cup-are reshaping how we think about infrastructure entirely. These events are not just about scale; they are about duration, distribution and resilience under constant pressure.
The Super Bowl has long been viewed as the ultimate peak event for sports betting. But even here, patterns are evolving.
Traffic no longer simply builds towards kick-off-it extends before, during and after. The operational window has widened, and so too have expectations placed on infrastructure.
And then comes the World Cup.
Unlike the Super Bowl, the World Cup is:
Rather than a single spike, it creates continuous, rolling demand across regions.
This is where the true challenge begins.
Scaling for a single peak is one thing. Designing for sustained, distributed engagement is quite another.
Operators must now rethink:
One critical takeaway is clear:
Infrastructure strain is driven by user volume and concurrency-not by individual high-value bets.
It’s not a handful of large wagers that push systems to their limits- it’s millions of users interacting simultaneously across markets.
Cloud adoption has transformed the industry- but it is not a cure-all.
Simply relying on hyperscale cloud providers does not guarantee resilience.
Instead, operators are increasingly adopting hybrid architectures, combining:
The objective is straightforward:
As Justin highlights, genuine resilience is achieved through careful design and planning-not technology alone.
As global sporting events grow in scale and complexity, infrastructure must evolve accordingly.
This means:
Because the next generation of betting moments will not just test systems over a few hours-they will test them continuously, worldwide and without pause.
For a deeper dive into Justin Cosnett’s perspective and Continent 8’s approach to managing global event infrastructure, read the full article in G3 Magazine: Read here
Enabling operators to scale across regulated markets with consistent, distributed data infrastructure across AWS Outposts, hybrid cloud, and Kubernetes environments
Continent 8 Technologies, a leading provider of managed IT solutions for the global iGaming and online sports betting industry, today announced the launch of its fully managed CockroachDB service. The offering expands Continent 8’s portfolio across AWS Outposts, hybrid cloud, and Kubernetes environments including AWS EKS – enabling operators and suppliers to deploy distributed, highly resilient data infrastructure.
The iGaming industry is entering a new phase defined by rapid scale, real-time player interactions, and increasingly complex regulatory requirements. Operators must support high-throughput transactional workloads across regulated markets while adhering to strict data sovereignty and compliance mandates – from the U.S. in each individual regulated state to country-specific regulations worldwide. At the same time, traditional monolithic databases are being pushed beyond their limits, struggling to scale dynamically and operate consistently across modern, distributed environments.
CockroachDB’s cloud-agnostic and PostgreSQL-compatible distributed architecture directly addresses these challenges by enabling strongly consistent transactions across regions and hybrid deployments. This allows operators to operate across markets while maintaining strict control over where data resides and how it is managed. Combined with Continent 8’s global footprint – spanning more than 100 locations across the globe in regulated jurisdictions – the service provides a foundation for deploying infrastructure closer to players without compromising compliance or performance.
“Continent 8 has always focused on delivering infrastructure that meets the unique demands of the iGaming industry – where performance, compliance, and uptime are non-negotiable,” said David Brace, Chief Alliance & Partnership Officer, AWS, at Continent 8 Technologies. “As our customers grow across regulated markets, the database becomes a critical component. Our managed CockroachDB service provides the consistency, resilience, and deployment flexibility required to support that growth.”
As operators scale into new markets and adopt hybrid deployment models spanning on-premises, cloud, and edge environments, the need for integrated, multi-region infrastructure continues to grow. By incorporating CockroachDB into its portfolio of hosting, cloud, connectivity, and cybersecurity solutions, Continent 8 delivers a unified platform designed to simplify operations while supporting massive scale in regulated environments.
“Partnerships like this are critical as operators move toward more integrated, ecosystem-driven infrastructure models,” said Allen Terleto, VP Global Partners and Ecosystem at Cockroach Labs. “By combining Continent 8’s managed services and AWS expertise with CockroachDB’s distributed SQL capabilities, we’re enabling customers to build and operate modern applications across hybrid environments with greater flexibility and control. It also strengthens the broader ISV ecosystem supporting iGaming, making it easier to bring new services to market on a data platform that can scale with the evolving demands of the industry.”
For more information on CockroachDB and Continent 8 please visit: https://www.cockroachlabs.com/partners/locator
From infrastructure to compliance, artificial intelligence is transforming gambling’s operational backbone. Continent 8 Technologies’ chief data, information and AI officer Cris Kuehl tells iGamingBusiness how the technology is unlocking major efficiency gains.
The influence and reach of artificial intelligence (AI) is growing rapidly in the gambling industry.
Until now, though, much of the attention has focused on player-facing tools that sharpen marketing campaigns and personalise experiences. After all, tangible, revenue-generating applications of the technology – from tailored promotions and recommendation engines to dynamic odds – are relatively straightforward to measure.
However, arguably the greatest impact is behind the scenes, with the technology becoming indispensable for improving efficiency and reducing costs. Indeed, this deployment of AI across this operational layer, which spans infrastructure, monitoring, compliance and internal services, is transforming how gambling businesses function at scale.
“The industry conversation gravitates towards the player-facing AI because the outcomes are visible and commercially intuitive,” says Continent 8 chief data, information and AI officer Cris Kuehl. “But the operational side is where AI delivers the most structurally significant efficiency gains, and it is considerably underinvested relative to its potential.”
Given the scale at which gambling platforms operate, AI is playing a vital role in analysing the data, logs, metrics, alerts and network telemetry underpinning each business. It would be impossible for a human to perform such tasks simultaneously.
“AI-driven operations help with initiating some automated remediations, and I think that’s key,” Kuehl says.
“The cost reduction there is very real, but it’s also more significant to gain resilience, catching degradation before it becomes an outage.
“Right now, we’re seeing a lot of AI use as a cost savings tool, but I like to look at it as a cost preventative measure. Outages are massive from a revenue loss perspective alone.”
As gambling businesses expand into new jurisdictions, regulatory requirements become increasingly complex.
AI is well suited to the challenges of ensuring compliance with regulations by automating structured, rule-based processes. This enables operators to scale more efficiently while maintaining consistency and accuracy.
“Compliance operations is a core component [of AI’s ability to improve infrastructure efficiency],” says Kuehl.
“The regulatory overhead of running a multi-jurisdiction iGaming business is massive. It’s substantial.
“The reporting, the audit trail management, monitoring, the data retention, enforcement – all of these are largely structured rule-based processes with high volume and load tolerance for error.
“This is not only well suited but designed to be AI assisted. Automation and the efficiency gains compound as the number of active jurisdictions continues to grow.”
The impact of AI extends beyond infrastructure into customer support, with these traditionally resource-intensive functions undergoing substantial change.
The conventional model relies on large agent pools, high attrition and reactive ticket management. It also struggles to scale efficiently across time zones, making it both costly and inconsistent. As a result, every new jurisdiction adds different language requirements or regulatory context that compounds the headcount cost.
However, AI can handle a significant portion of enquiries such as account questions, payment status, bonus mechanics and general troubleshooting.
“AI can handle those without any human involvement at all,” says Kuehl. “The proportion varies obviously by implementation quality and query complexity, but the biggest thing is it can consistently reduce agent volume requirements materially.
“I’ve seen it first-hand for the last five years – the transformation effort since COVID – and I think it’s only getting more and more aggressive.”
Agent augmentation is another key feature of AI’s impact on the customer support aspect of operations. With AI now able to handle the more menial tasks, a significant proportion of internal IT incidents can be resolved without a ticket escalation, leaving humans to focus on making a difference in other areas.
“This is great because mean time to resolution basically drops to nothing,” Kuehl says. “Repeat incidents decrease as root cause analysis continues to improve, and then my favourite part is that time is protected for the work that actually requires it. And I think this is absolutely huge.”
One of AI’s most valuable contributions is how it can enhance monitoring and therefore efficiency.
Companies like Kuehl’s Continent 8 can amass tens of thousands of alerts, sometimes for minor incidents.
AI can distinguish genuine anomalies from normal variance, allowing for an operations team to focus its attention where it is actually needed.
Another area where AI plays a key role is in predictive failure identification due to its pattern recognition ability across historical incident data, telemetry and vendor signals.
All of these can identify degradation patterns and trajectories before they produce an actual outage, bringing a clear financial value.
For Kuehl, automated correlation and root cause acceleration is another core way that AI is changing the type of intelligence and insight that managed service providers can deliver to customers.
“The reporting, the audit trail management, monitoring, the data retention, enforcement – all of these are largely structured rule-based processes with high volume and load tolerance for error.
“This is not only well suited but designed to be AI assisted. Automation and the efficiency gains compound as the number of active jurisdictions continues to grow.”
“Complex incidents are in a distributed environment involving signals across multiple different layers,” he says.
“You have the application layer, the network layer, the infrastructure layer and the security layer. AI-driven correlation platforms can assemble that picture faster than a human analyst can and even somebody who’s been working in this industry for decades.
“It’s not a replacement. It’s allowing them to actually use their brainpower in the right way and letting AI augment that to compress the time and the detection to resolution. I think that that’s key.”
Despite its benefits, AI introduces inevitable challenges.
Hyper-personalisation, for example, can enhance user engagement, but equally raises concerns about encouraging excessive gambling and potentially breaching data privacy laws.
For this reason, having a human in the process to ensure adequate oversight is essential, with clear audit trails, escalation mechanisms and accountability frameworks all important when using AI.
“The governance consideration that matters here is how AI handles the customer interactions in iGaming,” Kuehl says. “They are going to be extremely important because they touch the regulated activities, including responsible gaming complaints, KYC queries and payment disputes, for example.
“This audit trail and escalation logic has to be built in, and whether you’re deploying a customer-facing AI agent or an IT system, doing so without the appropriate governance architecture is regulatory suicide.”
While much of the conversation around AI focuses on technical capability, such as data science, prompt engineering and model development, a more limiting knowledge gap is business-side AI literacy.
Another knowledge gap that is holding back operators, according to Kuehl, is AI governance capability, meaning the ability to design and operate a model risk framework and maintain audit trails.
Furthermore, one of the most common mistakes when it comes to designing, implementing and managing IT infrastructure and security with AI is treating security as a compliance exercise rather than an operational priority.
“Designing a security posture around passing audits that produces a documented environment that may not be materially secure,” says Kuehl.
“Genuine security requires continuous operational investment, threat monitoring, vulnerability management and incident response rehearsal. I think that’s the biggest mistake iGaming businesses are making. After all, this industry is one of the most attacked!”
AI is transforming the gambling industry, but one of its biggest impacts is taking place under the surface.
While player-facing applications are scrutinised and noticed the most, it is the operational side of monitoring, infrastructure, compliance and support that is being remodelled.
As the industry continues to evolve, those who successfully integrate AI into their core operations will have a huge advantage over those who do not.
Learn more about it, in the iGaming Business report. Read the full report here.
Continent 8 Technologies, a leading provider of cuttingedge managed IT solutions designed for the global iGaming and online sports betting industry, announces the appointment of Cris Kuehl as its Chief Data, Information and AI Officer.

Cris brings more than 20 years of experience in enterprise AI, analytics, and data strategy, making him a powerful addition to Continent 8’s leadership team. He joins the company with an extensive background in senior leadership roles, including serving as Vice President of Artificial Intelligence & Data Science at Akkodis and Global Head, VP, CX Analytics & AI at Foundever.
Cris has built a career helping highly regulated organisations adopt secure, scalable and practical AI capabilities, and his leadership will accelerate Continent 8’s mission to deliver intelligencedriven, futureproof infrastructure and cybersecurity solutions.
In his new role, Cris will lead the company’s global data, AI, and information strategy – driving innovation across analytics, automation, cybersecurity resilience, and customercentric intelligence. His remit includes shaping Continent 8’s AIenabled product evolution, championing responsible AI practices, and strengthening data governance frameworks aligned with the needs of the iGaming, tribal, and enterprise sectors.
“Cris’ deep expertise across data, AI, and regulated environments is an exceptional match for our organisation’s direction,” said Michael Tobin, CEO and Founder of Continent 8 Technologies. “As the industry rapidly shifts toward intelligencedriven infrastructure, his leadership will ensure we continue to provide secure, highperformance solutions that deliver measurable value to our customers.”
“I’m thrilled to join Continent 8, a leader in its field, at such a pivotal moment,” said Cris Kuehl. “AI is transforming how organisations operate, collaborate, and protect their data. Continent 8 is uniquely positioned to lead this transformation for the global iGaming and online sports betting sector. I’m excited to help drive the next chapter of innovation.”
In the latest episode of Continent 8’s Ask the Expert podcast series, Craig Lusher, Principal Solutions Architect, sits down with Elizabeth Grima, Senior Executive Manager at New Dawn Risk, to unravel one of the most misunderstood – but increasingly critical – areas of iGaming resilience: cyber insurance.

Both experts have spent years helping operators navigate real-world incidents that strike without warning – from ransomware to payment fraud, account takeovers, and vendor outages. Their message is clear: cyber insurance is no longer optional – it’s a core component of operational continuity for any iGaming business.
If you haven’t had time to watch the podcast episode, below is a summary of the episode’s key takeaways.
The iGaming sector is one of the most attractive global targets for cybercriminals. High‑value financial transactions, player data, round‑the‑clock uptime requirements, and interconnected vendor ecosystems create a perfect storm of cyber risk.
Cyber insurance helps operators withstand these threats by providing a financial safety net – but also much more. Modern policies include:
This combination ensures operators can recover faster, smarter, and with less long‑term damage.
When a breach or outage occurs, every minute matters – and every minute is costly. Cyber insurance helps operators rapidly mobilise the right resources by covering:
This dual support – financial and operational – means operators can focus on restoring service and protecting players, rather than scrambling to fund or coordinate a crisis response.
A persistent misconception in the industry is that strong cybersecurity reduces the need for insurance – or vice versa.
In reality, the two work hand in hand:
Insurers increasingly expect baseline controls before offering coverage, including MFA, backups, monitoring, and social‑engineering safeguards.
Businesses that demonstrate strong cyber maturity often receive better pricing, fewer exclusions, and higher coverage limits.
Not all losses are automatically covered. Operators must pay close attention to key policy conditions:
Ensuring internal teams understand these requirements is essential for maximising protection.
Craig and Elizabeth highlight several myths that continue to cloud decision‑making across the industry:
Consider two of the most common (and costly) incidents:
An operator suffers a sustained DDoS attack during a major sporting event. Impacts include:
With cyber insurance, expert teams rapidly intervene, reduce downtime, and help restore services – while the insurer covers response and recovery costs.
When sensitive player data is exposed, expenses skyrocket:
Cyber insurance helps manage the fallout and protects the operator’s reputation.
To address the growing needs of iGaming operators, Continent 8 and New Dawn Risk have partnered to deliver a unified, industry‑specific cyber defence and insurance solution.
The partnership offers:
By combining Continent 8’s multi‑layered cyber protection with New Dawn Risk’s specialist insurance expertise, operators gain a comprehensive solution designed specifically for their operational and regulatory environment.
In an industry where downtime directly translates into lost revenue – and lost trust – cyber insurance has become a fundamental layer of resilience.
By integrating:
… iGaming operators can withstand today’s evolving threats with confidence.
The Continent 8 and New Dawn Risk partnership ensures that operators are not only protected – but empowered – to operate securely across multiple jurisdictions.
Watch episode 7 of Continent 8’s Ask The Expert podcast featuring New Dawn Risk
Continent 8 Technologies, a leading provider of cutting-edge managed IT solutions designed for the global iGaming and online sports betting industry, has entered into a strategic partnership with New Dawn Risk, a specialist Lloyd’s broker.
This collaboration brings together Continent 8’s cybersecurity services with New Dawn Risk’s insurance expertise to offer iGaming businesses a coordinated approach to risk management. Operators benefit from both enhanced security protection and reduced insurance premiums, with underwriters offering discounts based on the security maturity and controls in place.
“This partnership represents a significant step forward in how we support our clients,” said Elizabeth Grima, Senior Executive Manager, New Dawn Risk. “By combining Continent 8’s trusted cybersecurity services with our tailored insurance solutions, we are offering iGaming companies a truly end-to-end risk management package. It goes beyond traditional broking – it’s about delivering resilience, continuity, and peace of mind in a sector where cyber threats and regulatory pressures are constantly evolving.”

The new offering will initially launch in the UK and Europe, with plans to expand globally. It combines specialist cybersecurity services with tailored insurance to make protection more accessible to iGaming companies. Services include Managed SOC & MDR, Cyber Threat Intelligence Exchange, DDoS protection, Web Application and API Protection (WAAP), and Multi‑Factor Authentication (MFA) for end users. Businesses adopting the package will benefit from discounted premiums, which increases their access to cost effective coverage.
“We are excited to partner with New Dawn Risk,” said Patrick Gardner, Chief Security Officer at Continent 8 Technologies. “This collaboration brings together two specialists in their fields to offer a compelling mix of advanced cybersecurity controls and tailored insurance solutions for the iGaming industry. Strong cyber defences not only protect operators and suppliers but also demonstrate sound risk management – an increasingly important factor when it comes to reducing insurance premiums. As the go-to cybersecurity provider to the industry, we’ve been delivering multi-layered protection solutions to high-risk gaming businesses for years, and this partnership builds on that proven foundation.”

Blueprint Gaming is a leading UK-based game studio and part of Germany’s Gauselmann Group. The company develops innovative slot games for the global online and mobile markets, with titles also available across more than 100,000 land-based gaming terminals in the UK, Germany, and Italy.
Blueprint Gaming had been using an incumbent SIEM tool that offered technology but not the expertise and operational support of a fully managed SOC.
As a lean infrastructure team operating in a high-risk, data-intensive industry, Blueprint needed:
Without additional specialist resources, maintaining a proactive security posture was becoming increasingly challenging.
Blueprint selected Continent 8’s Managed Security Operations Centre (MSOC) — a complete, fully managed security service integrating an advanced SIEM platform operated by Continent 8’s cybersecurity specialists.
Key capabilities delivered included:
This combination of technology, people, and process provided the 24/7 monitoring and threat response Blueprint required – without increasing internal workload.
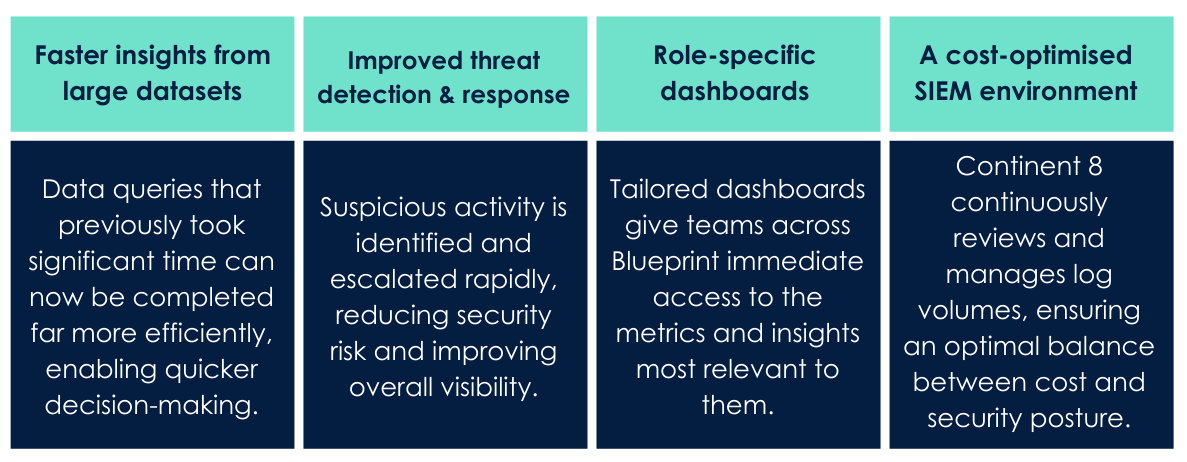
Continent 8 delivered a robust managed security solution combining a leading technology stack with expert cybersecurity professionals who operate and manage the environment on Blueprint’s behalf.
Outcomes included:
Adam Shepherd, Head of Infrastructure at Blueprint
“We’re a small team that manages huge volumes of data in a high-risk industry. Managing that effectively – without compromising security – was a real challenge for us. That’s where Continent 8 stepped in, providing a managed SOC service with a strong focus on the threat landscape. They’ve enabled quicker responses to threats and equipped us with simplified dashboards. Working with the team has been a real pleasure.”
Patrick Gardner, Chief Security Officer at Continent 8
“Blueprint required strong security oversight without adding operational burden to a lean internal team. Our Managed SOC service was designed to deliver exactly that – improving visibility, accelerating threat detection, and optimising log volumes while maintaining a robust security posture. The result is a scalable, cost-efficient security capability aligned to the realities of a high-risk, data-intensive environment.”
Click to download the PDF version
Cybersecurity regulation in Europe is evolving rapidly, and iGaming businesses must prepare now for two major incoming frameworks: the NIS2 Directive and the EU cyber resilience act (CRA). These regulations introduce stricter security obligations, tighter reporting deadlines and heightened accountability across the iGaming ecosystem.

In our recent webinar, “iGaming’s new cybersecurity rules”, Oliver Crofton (Regional Sales Director – Cybersecurity at Continent 8 Technologies) hosted an in‑depth discussion with Craig Lusher (Principal Solutions Architect EMEA at Continent 8 Technologies) and Jo Joyce (Partner and Head of Regulatory, IP & Digital at Taylor Wessing Ireland). Together, they provided clarity on the regulatory landscape and outlined what operators, suppliers and technology partners must do to stay ahead.
Here’s a breakdown of the key takeaways.
The iGaming industry operates in a high‑risk digital environment. Real-time financial transactions, complex technology stacks, and large volumes of sensitive personal data (including government-issued identity documents attached to financial information) make it a prime target for attackers. As cyber threats grow more sophisticated, regulators are raising the bar to ensure resilience.
NIS2 and the CRA aim to:
For iGaming, where uptime, trust and compliance underpin commercial success, these changes are significant.
NIS2 is fully live and enforcement has begun. This is no longer about preparation; the question is whether your organisation is compliant right now.
According to Craig and Jo, NIS2 represents a major overhaul of Europe’s cybersecurity framework. It replaces the original NIS Directive (2016), which was fragmented, voluntary in practice, and allowed each country to implement it differently.
Key updates include:
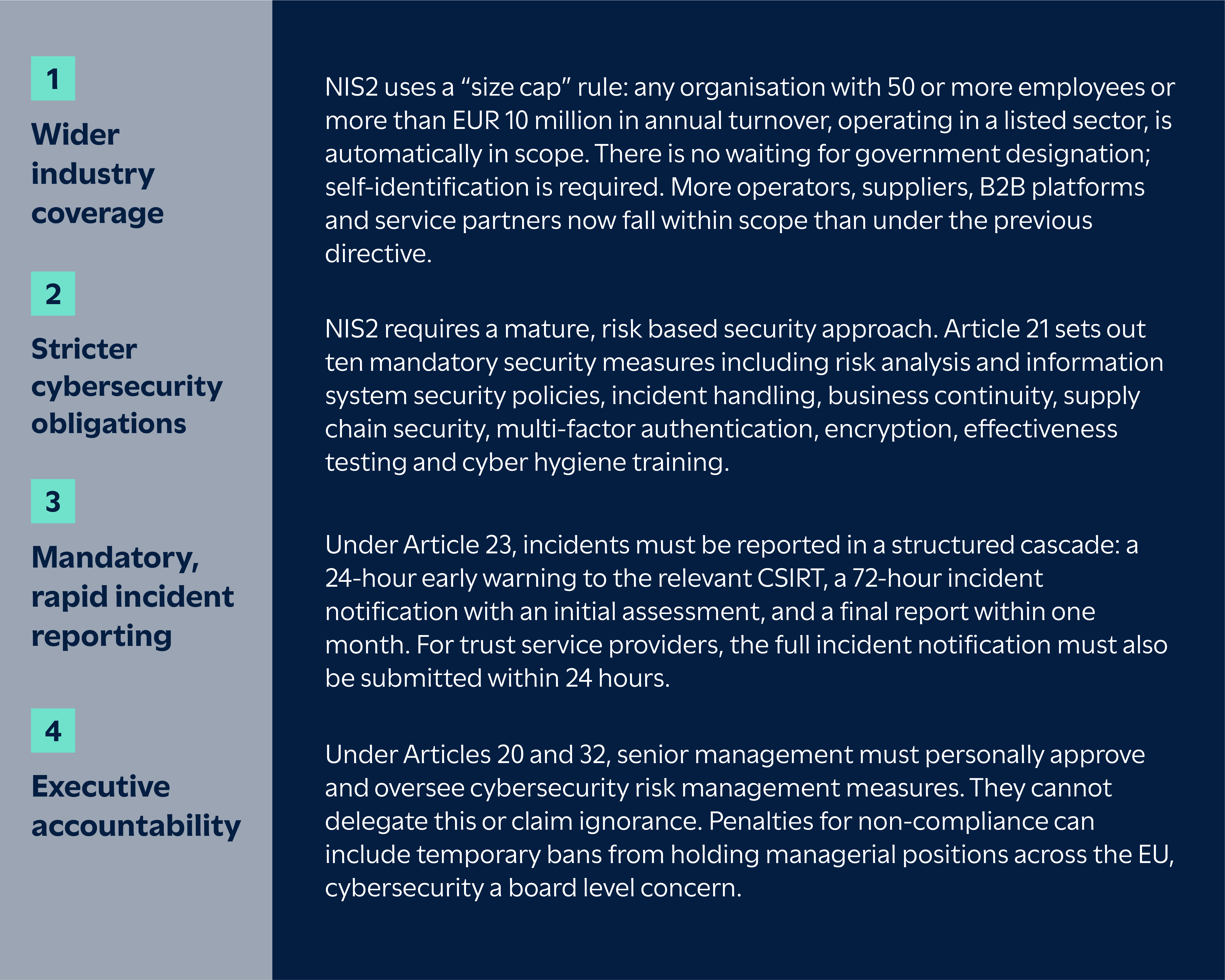
Whilst NIS2 focuses on how organisations manage security, the CRA concentrates on the digital products those organisations depend on and produce.
CRA reporting obligations begin on 11 September 2026. From that date, manufacturers must report actively exploited vulnerabilities and severe incidents affecting the security of their products, following the same 24-hour early warning, 72-hour notification structure. For vulnerabilities, the final report must be submitted within 14 days of a corrective measure becoming available. Full product standards, including CE-marking requirements for software and connected devices, come into force in December 2027.

Jo highlighted that the CRA requires manufacturers and developers of digital tools – including gaming software, APIs, hardware and integrated systems – to
Given the heavy reliance on third‑party tech in iGaming, this places strong emphasis on vendor due diligence and supply‑chain oversight.
Jo: “I think one of the things that I’ve spotted is quite a lot of operators and firms within the iGaming ecosystem haven’t really necessarily accepted that they’re in scope.”
If your organisation provides or supports any of the following, NIS2 likely applies:
There are two additional points worth flagging. First, white-label and B2B providers are often managed service providers (MSPs) without realising it. If you run a player account management (PAM) system for 20 other brands, you are managing their core services, which, by definition, makes you an MSP. Under NIS2, MSPs are designated as essential entities, meaning they face ex ante supervision (proactive inspections and audits at any time), the same regulatory tier as a data centre or cloud provider.
Second, there is no “group privilege” under NIS2. If an internal IT arm provides services to the wider corporate group, it may be classified independently as an essential entity in its own right. Being part of a larger group does not shield individual subsidiaries or divisions from independent classification.
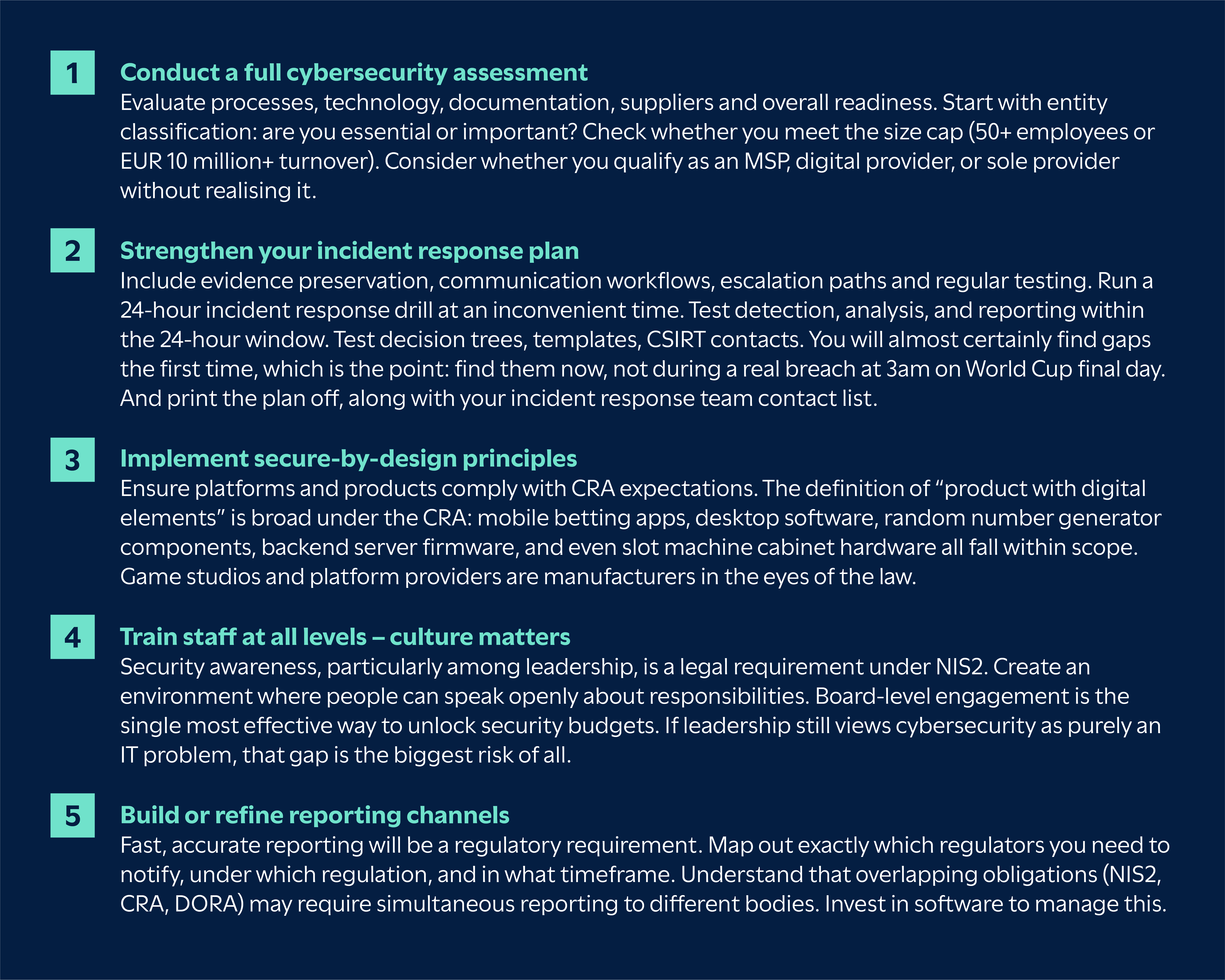
A readiness assessment is the essential first step.
Craig emphasised how the threat landscape facing iGaming businesses has intensified – including a 400% surge in cyber attacks targeting the gambling industry. This is not a gradual trend; attackers have industrialised their approach.

Operators and suppliers now face:
The interconnected nature of the sector amplifies the impact of any single vulnerability.
The cost of downtime in the industry now exceeds $6,000 per minute, and attacks are more visible in the news than ever, and recent breaches have seen hundreds of thousands of user profiles and identity documents exposed through relatively basic misconfigurations.
Craig highlighted several country‑specific differences in how NIS2 is being implemented, here are a few examples:
Malta moved faster than most EU member states, issuing Legal Notice 71 of 2025, with the CIPD as the ‘competent authority’. Self‑registration was due September 2025, so organisations that missed the deadline are now operating in a regulatory grey area. Governance and risk‑management controls must be live by March 2026, which at the time of the webinar was just weeks away.
Malta also goes further than EU baseline requirements by mandating a 24/7 security operations centre for digital infrastructure providers. Properly staffing a round-the-clock SOC requires at least 12 people to maintain a true rotation, which is a substantial operational investment for mid-sized operators.
The ultimate sanction isn’t just a fine; Malta can suspended MGA licences. For Malta-licensed gaming companies, this is an existential threat. If you lose your MGA licence, you are effectively locked out of dozens of global markets overnight.
Germany passed its implementation late, in November 2025. Registration deadlines for German‑based entities land in April 2026, leaving limited time for compliance.
Other member states are at various stages of transposition, and several missed the original October 2024 deadline. For operators with a presence in multiple EU countries, the practical challenge is managing compliance against several different national timelines and requirements simultaneously.
NIS2 is an EU directive, which means each member state must transpose it into national law. The result is that implementation timelines and specific requirements vary from country to country, and organisations operating across multiple jurisdictions need to track each one independently.
Both speakers stressed that NIS2 and the CRA require visible, ongoing engagement from senior management. Leading organisations will:
Under NIS2, leadership accountability is explicit. Executive training is not optional; it is a legal requirement under the directive.
Jo: “Just because something bad has happened doesn’t mean that you’re necessarily at fault… but you are going to have to produce reasonable reporting in layman’s terms… and explain that we’re operating in different risk parameters.”
Craig added the importance of training: “It’s mandatory for board‑level staff… you’ve got to keep training and constant training.”
Craig and Jo discussed the importance of reporting – especially when something goes wrong.
Jo: “The kind of reporting that one has to do under NIS2 is not a million miles away from the pre‑existing reporting… but there’s a real shift when you are experiencing a very serious incident.”
The 24‑hour reporting window is the operational flashpoint. Many companies are not ready for this. Under NIS2, the clock starts as soon as you become aware of a significant incident. You then have 24 hours to submit an early warning to the relevant CSIRT, 72 hours for a more detailed incident notification, and one month for the final report. A single incident can also trigger reporting obligations under the CRA and DORA simultaneously, each with different data requirements, formats, timelines and regulators.
Businesses need to prepare now by having supplier lists to hand, knowing exactly where to submit reports for each applicable regulation, and understanding that multi-jurisdictional reporting may be required.
Top tip from Jo:
Please print out a copy of your breach response plan… print out your incident response team list with phone numbers, ideally personal ones. If you can’t access your systems, it will take you an astonishing amount of time to pull this together.
Jo highlighted that enforcement activity under the CRA and NIS2 will be phased but increasingly serious.
From September 2026, the CRA introduces mandatory reporting of actively exploited vulnerabilities and severe incidents affecting product security. Full product‑related obligations take effect in December 2027, including the requirement for CE‑marking digital products, software included.
According to Jo, failure to report will likely be the first area where regulators take action, and penalties will be treated seriously.
Many NIS2 requirements are already enforceable. For essential entities that breach Articles 21 or 23, fines can reach up to EUR 10 million or 2% of total worldwide annual turnover, whichever is higher. For important entities, the maximum is EUR 7 million or 1.4% of worldwide turnover (Article 34 of NIS2). Regulators also have the power to issue binding instructions, order security audits, and, for essential entities, temporarily suspend or prohibit individuals from exercising managerial functions (Article 32(5)).
Jo: “They will factor in whether it’s going to bankrupt you… but they want these fines to hurt.”
This means businesses must act now to ensure reporting pathways, governance structures, supplier oversight and security controls are ready.
Craig and Jo recommended several clear actions for organisations:
There is a growing issue around the use of open‑source software (OSS) under the CRA. Although many OSS developers lobbied for exemption, OSS is widely used in commercial products. The CRA makes clear that organisations relying on OSS within regulated products remain fully responsible for meeting all cybersecurity and update obligations, including providing security updates for the minimum five-year support period.
Managing updates is difficult when you did not write the code – but the responsibility remains. The Software Bill of Materials (SBOM) requirement compounds this: manufacturers must maintain a machine-readable inventory of every library, open-source component and module in their products, kept as a living record.
Top tip from Jo:
If your business relies heavily on OSS, pay close attention to how it’s managed, seek specialist guidance and plan how you will meet long‑term update and security requirements.
The introduction of NIS2 and the EU cyber resilience act marks a significant shift for cybersecurity in iGaming. While the regulations bring real compliance challenges, they also create an opportunity for the industry to strengthen its defences, reduce operational risk and future‑proof operations.
Early preparation will help businesses stay compliant, competitive and trusted.
👉 Watch the full webinar here: