

In cybersecurity, intelligence is power. Financial institutions and healthcare providers have long relied on threat intelligence platforms to anticipate attacks and protect critical assets. Yet, the gambling industry, despite handling billions in transactions and sensitive customer data, has been slower to adopt this proactive approach.
The stakes are high. Cyber incidents targeting gaming operators have surged dramatically, with attacks becoming more sophisticated and financially devastating. We have seen land-based casinos forced offline for days.
For an industry built on trust and real-time engagement, the question is no longer whether operators need intelligence, but how quickly they can integrate it into their security posture.
Consider financial services. Banks operate under constant threat from fraud, phishing, and ransomware, yet they’ve built robust intelligence-sharing ecosystems like FS-ISAC (Financial Services Information Sharing and Analysis Center). These platforms allow members to share threat intelligence in real time, creating collective defence that benefits the entire sector.
Gaming needs its own equivalent, but with crucial differences. Our adversaries are unique: organised crime groups targeting high-roller accounts, bonus abuse rings operating across dozens of operators, match fixers probing betting platforms, and in certain jurisdictions, nation-state actors targeting offshore operations. Generic threat intelligence platforms miss approximately 70% of gaming-specific attack patterns because they weren’t designed to recognise these threats.
Effective threat intelligence transforms security operations across several critical areas.
Smarter vulnerability management:Gaming operators run complex technology stacks spanning payment processors, gaming engines, live betting platforms, and player databases. Patching everything according to generic severity scores is impossible during live operations. Intelligence changes the equation from “how severe could this be?” to “is this being actively exploited against gaming platforms now?” When intelligence reveals a payment gateway vulnerability under active exploitation against European operators, that patch moves to the front of the queue regardless of theoretical severity.
Faster incident response:Intelligence enables teams to build playbooks for gaming-specific scenarios before incidents occur. When attacks happen, context accelerates decisions. A generic PowerShell alert becomes high priority when intelligence identifies it as a technique used by gaming-targeting ransomware groups. The MITRE ATT&CK framework provides common language for this intelligence, allowing teams to measure defensive coverage objectively and identify gaps systematically.
Example: Champions League final, an operator detected unusual API calls to their odds calculation engine. Intelligence immediately revealed the same pattern had appeared at three other sportsbooks in the preceding 48 hours. A pre-built playbook isolated affected systems automatically. The attack was contained in four minutes rather than 45.
Proactive threat hunting:Shared intelligence generates hunting hypotheses no single operator could develop alone. When multiple operators detect reconnaissance against payment systems using specific techniques, everyone can search for identical indicators. Security teams shift from reactive firefighting to actively hunting for bonus abuse automation, payment fraud patterns, and early reconnaissance.
Reduced alert fatigue:Gaming platforms generate millions of security events daily. Intelligence-driven contextualisation transforms “this IP attempted 50 logins” into “this IP is part of a credential stuffing botnet that hit six gaming sites today.” Alerts receive priority based on actual gaming industry impact. Analysts escape false positive overload and focus on genuine threats.
Intelligence extends beyond traditional cybersecurity. iGaming’s ecosystem of platform providers, payment processors, and affiliate networks creates significant supply chain risk. When a major provider suffers a breach, operators need immediate notification and indicators to hunt for compromise in their own environments.
Fraud prevention benefits enormously from shared intelligence. Credential stuffing, bonus abuse rings, and synthetic identity creation operate across multiple operators simultaneously. Real-time sharing allows the entire industry to block known fraudsters before they cause widespread damage.
iGaming operates under intense regulatory scrutiny across multiple jurisdictions. Intelligence programmes must account for data sovereignty when sharing across borders, maintain evidence chains for incident reporting, and demonstrate due diligence to regulators.
Rather than complicating compliance, intelligence sharing strengthens it. Documented participation demonstrates proactive security investment. Standardised incident categorisation streamlines reporting. Cross-operator intelligence identifies systemic risks that regulators will certainly notice even if individual operators miss them.
None of this works without trust. Operators compete fiercely, and sharing incident details raises legitimate concerns about competitive exposure.
Effective programmes offer anonymity where needed – operators can share indicators without identifying themselves. Clear data governance establishes who accesses what information. Critically, the value must be obvious. Operators need to see that participation makes them measurably safer, that what they receive far exceeds what they contribute. As membership grows, network effects compound: more operators sharing means better intelligence for everyone.
Gaming operations run around the clock with no maintenance windows during major sporting events. Attacks deliberately target peak revenue periods. Response times measured in hours are unacceptable.
This demands SOAR (Security Orchestration, Automation & Response) automation. When intelligence identifies malicious infrastructure, indicators must flow automatically into firewalls and detection systems. Pre-configured playbooks must execute without waiting for human intervention.
Operators with mature programmes report mean time to detect dropping from 14 hours to under 10 minutes. Mean time to respond falls from four hours to 12 minutes. False positives reduce by 70%.
With average gaming breach costs exceeding $5M including regulatory fines and customer compensation, preventing one major incident justifies significant investment. When a zero-day in payment gateway software was identified through shared intelligence, operators with access isolated vulnerable systems 48 hours before public disclosure. Those without suffer breaches averaging $5M each.
The gaming industry has reached an inflection point. We can continue operating in silos, or recognise that collective defence serves everyone’s interests. The attackers are already collaborating; we must do the same.
Financial services learned this lesson years ago. For gaming, the question is whether we learn proactively or wait for a sector-wide incident to force the conversation.
For more information on Threat Exchange, visit continent8.comor email sales@continent8.com.
**Source: EGR Digital Edition 248
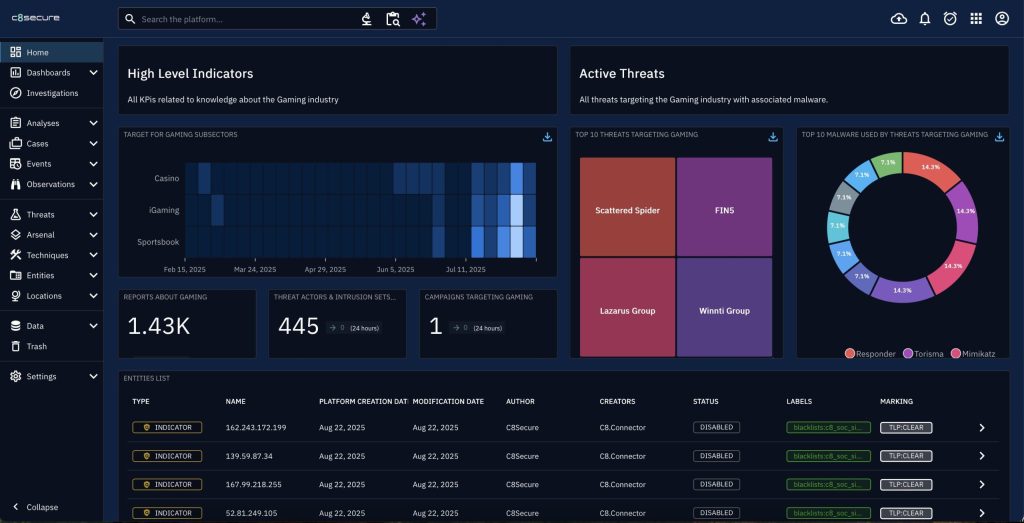
As the iGaming and online sports betting industry faces increasingly sophisticated cyber threats, Continent 8 is proud to launch Threat Exchange – the sector’s first dedicated cyber threat intelligence (CTI) platform.
Below, we answer some of the most pressing questions regarding the solution and how it is tailored for incident response teams, operators, platform providers, B2B gaming technology companies and regulators.
A cyber threat intelligence (CTI) platform collects, analyses and shares information about current and emerging cyber threats to help organisations anticipate, detect and respond to attacks more effectively. It typically includes:
CTI platforms are essential for building a proactive security posture, especially in high-risk industries like iGaming and online sports betting.
Threat Exchange is a managed cyber threat intelligence platform designed specifically for the iGaming and online sports betting industry. It delivers real-time, sector-specific insights to help incident response teams, operators, platform providers, B2B gaming technology companies and regulators detect and share information on emerging threats, sharpen awareness and act with confidence.
Unlike generic CTI solutions, Threat Exchange is purpose-built for iGaming. It leverages Continent 8’s and C8 Secure’s unique position as both an internet service provider (ISP) and managed security service provider (MSSP) in the industry, offering exclusive intelligence, real-time threat correlation and honeypot-driven insights tailored to gaming environments.
Threat Exchange addresses the following critical challenges:
Cyber Threat Exchange’s key features include:
Whether you’re protecting high-value player accounts, monitoring threats during major sporting events or securing gaming APIs, Threat Exchange is designed to meet the needs of the industry. The solution is suitable for:
Threat Exchange offers several tiers, from a community tier with basic access to advanced tiers with predictive analytics and premium add-ons. Each tier is designed to meet different operational needs and cybersecurity maturity levels.
It’s important that businesses take a multi-layered approach to cybersecurity to ensure full protection. Add-on services include:
We’re excited for the launch but we’re already looking to the future. Developments include:
Contact your Continent 8 account manager or visit Threat Exchange to request a demo, explore pricing tiers and see how Threat Exchange can elevate your cybersecurity posture.
Continent 8’s end-to-end regulatory cybersecurity services ensure Rising Digital maintains full compliance within the six – and growing – US states in which it operates.

Rising Digital Corporation is a gaming company that develops and publishes slot games, table games, game systems and game platforms. Recognized as the leading developer of Asian slot games in the casino gaming industry, Rising Digital provides games to the major gaming manufacturers worldwide.
Rising Digital required a Managed Security Service Provider (MSSP) to architect and deploy regulatory compliance programs tailored to the diverse requirements of each interested US state jurisdiction, ensuring consistent, best-in-class security and regulatory standards across all operational states.
Rising Digital selected Continent 8, its existing cloud partner and the leading provider of infrastructure and cybersecurity solutions for the iGaming and online sports betting sector, to lead its regulatory cybersecurity strategy.
In collaboration with Continent 8 and its cybersecurity specialist division, C8 Secure, Rising Digital successfully completed a comprehensive suite of regulatory compliance assessments and services, including:


Rising Digital has successfully rolled out a comprehensive cybersecurity program across multiple jurisdictions, including Connecticut, Delaware, Michigan, New Jersey, Pennsylvania and West Virginia – as well as the Canadian province of Ontario – delivering compliance with state-specific requirements. In addition, Continent 8’s regulatory cybersecurity expertise has enabled the proactive identification of vulnerabilities and the delivery of actionable insights that fortify Rising Digital’s cybersecurity posture.
By partnering with Continent 8 and leveraging its regulatory cybersecurity services, Rising Digital is strategically positioned to proactively address and surpass evolving compliance requirements. This collaboration ensures a measurable competitive edge with regulators across both forthcoming US state market deployments and established jurisdictions.
Aimin Cong, CEO of Rising Digital, said: “We are delighted to formalize our relationship with Continent 8 for our growing iGaming operations business. With the utmost importance being placed upon compliance, performance and security, we believe Continent 8 is an excellent infrastructure and cybersecurity services partner.”
Patrick Gardner, Chief Security Officer at Continent 8, said: “We are honored that Rising Digital has placed its trust in Continent 8 as its infrastructure and cybersecurity partner as they expand their operations across the United States.
“At Continent 8, we pride ourselves as being a one-stop-shop provider of infrastructure, cloud, regulatory and cybersecurity solutions. Our services enable iGaming companies like Rising Digital to swiftly meet multi-state regulatory requirements, safeguarding their operations while providing peace of mind. We stand committed to setting the highest standards and value for cybersecurity and compliance services within the ever-growing iGaming and online sports betting sector.”
For more information on how to meet your jurisdiction’s regulatory cybersecurity requirements, visit continent8.com or contact sales@continent8.com.
Vulnerability Assessment and Penetration Testing (VAPT) service enables the independent gaming commission to test IT infrastructure for vulnerabilities
Continent 8 Technologies, the leading provider of managed hosting, connectivity, cloud and cybersecurity solutions for the tribal gaming industry, supports Cherokee Tribal Gaming Commission (TGC) with its proven Vulnerability Assessment and Penetration Testing (VAPT) services.
The Cherokee Tribal Gaming Commission is the independent tribal gaming regulatory authority established in 1993 under Chapter 16 of the Cherokee Code of the Eastern Band of Cherokee Indians (EBCI).Charged with the duty to ensure fairness and integrity of the gaming activities within its facilities, the commission enlisted Continent 8, and its cybersecurity division, C8 Secure, to conduct pen testing.

The VAPT service provides a comprehensive security assessment of an organizations infrastructure and applications. Often mandated by regulation, it helps organizations measure the real-world effectiveness of their security controls and incident response capabilities. Additionally, the service provides actionable insights, including prioritized recommendations and industry best practices to address identified vulnerabilities and strengthen overall cybersecurity posture.
Emra Arkansas, Executive Director at Cherokee Tribal Gaming Commission said: We are sincerely grateful to Continent 8, especially Patrick Gardner, Anthony Engel and Jerad Swimmer, for their partnership and recognition of our ongoing cybersecurity initiatives. The Cherokee Tribal Gaming Commission remains firmly committed to protecting not only our critical infrastructure but also the sovereignty that underpins our regulatory authority. In an era of growing cyber threats, safeguarding Tribal IT systems is more than a technical priority, it is a sovereign responsibility. With Continent 8s trusted expertise, we are proud to set a higher standard for cybersecurity in Indian Country, ensuring our operations remain secure, resilient and self-determined.
Patrick Gardner, Chief Security Officer at Continent 8 said:In response to todays evolving cyber threat landscape, the Cherokee Tribal Gaming Commission is working to establish a new standard in cybersecurity and we are proud to support this important initiative. Their proactive efforts to safeguard critical infrastructure reflect a deep and ongoing investment in cybersecurity resilience.”
Jerad Swimmer, Regional Sales Director at Continent 8 added: “It was a pleasure collaborating with the Cherokee Tribal Gaming Commission in conducting a comprehensive evaluation of their IT infrastructure. Their team has shown a tremendous awareness of the escalating cybersecurity challenges within the tribal gaming sector. It is encouraging to see both enterprises and regulatory authorities actively enhancing their cybersecurity measures.”
For more information on how Continent 8 can support your cybersecurity initiatives or to schedule a no-obligation Cybersecurity Readiness Consultation, contact Regional Sales Director, Jerad Swimmer, at jerad.swimmer@continent8.com.
Key highlights:
In the iGaming and online sports betting industry, where cybersecurity breaches can result in unauthorised access, identity theft, account takeovers, operational disruptions and reputational damage, MFA is an essential security measure. It’s also mandated for the regulated Brazilian iGaming market, where operators must submit proof of compliance.

In this blog, Luana Monje, Brazil-based Sales Executive at Continent 8 Technologies, explores the significance of MFA in Brazil’s exciting market, highlighting its role as both a regulatory cybersecurity requirement, outlining key considerations when selecting an effective authentication platform, and showcasing Continent 8’s passwordless MFA solution designed to deliver the most seamless single-step PIN experience.
According to the Secretariat of Prizes and Bets (SPA) and the Ministry of Finance’s (MF) technical and cybersecurity guidelines for Brazil’s betting systems (Ordinance No. 722, available in Portuguese), MFA is defined as:
A type of authentication that uses two or more of the following elements to verify a user’s identity: information known only to the user, such as a password, a pattern, or answers to challenge questions; an item owned by a user, such as an electronic token, a physical token, or an identification card; a user’s biometric data, such as fingerprints, facial or voice recognition.
First and foremost, Brazilian regulations require the implementation of MFA across several technical and cybersecurity requirements outlined in Ordinance No. 722. These requirements include:
Ordinance 722, Annex I, sections 12, 13 and 16 – Access to the betting system:
a) at least once every 7 (seven) days; or
b) on the first access after a period of inactivity of more than 7 (seven) days.
Ordinance 722, Annex IV, section 25f – Technical Controls, DNS requirements:
25 – The following requirements apply to servers used to resolve Domain Name System (DNS) queries in association with the betting system:
f) multi-factor authentication must be in place
MFA provides a layer of cybersecurity that significantly mitigates the risk of unauthorised access, thereby safeguarding sensitive data and personal information.
With MFA being a regulatory requirement in Brazil, iGaming and online sports betting operators need to evaluate which MFA options are most suitable for their operations. Here are some key considerations when assessing an MFA platform, and how Continent 8 can support your MFA journey.
| Key Consideration | The Continent 8 MFA Advantage |
|---|---|
| User experience | Same passwordless, 2-second, single-step login – on all devices and browsers
99.9% of users log in within 2 seconds. Supports biometric auth in apps. Our MFA solution ensures consistent user experiences across both app and browser platforms, while also offering the option of local biometric authentication for apps. |
| Compatibility / Operability | 100% of devices, 100% of browsersOur MFA solution ensures complete independence from hardware or operating systems, enabling compatibility across all devices and platforms.
By providing our solution through the same browser interface as the operator’s service, or by embedding the technology directly into the operator’s native app, we support:
|
| Login success rate | 99.93% login success or higherOur MFA platform streamlines the login process to a passwordless, single user step. The system is capable of operating with either a PIN or biometric authentication, providing users with flexibility and a reliable fallback across any device or browser.
Each additional step increases the potential for user error, and every dependency (such as downloads, installations, mobile phones, cellular networks, or username entry) introduces a potential point of failure for both users and the system. Our platform achieves a 99.93% login success rate in consumer-facing applications, using either a 4-digit PIN or device-based biometric authentication where available. Our platform also attains a 99.997% success rate in action (transaction) authentication. There is no difference in success rates between mobile and tablet/laptop devices, as the system does not rely on the presence of a mobile device. |
| Registration success rate | +18% in player registrations, 20% boost in profitsOur MFA solution’s enrolment process simply requires users to select a 4-digit PIN. This procedure does not require any permissions, downloads, plug-ins, imported keys or configurations, thereby eliminating registration failures. The enrolment can be completely invisible and take place during customer registration.
User process – on any device or browser:
The result: +18% increase in user registrations which can boost profits by up to 20%. |
| Support costs | 90% savings in support costs
Our MFA solution minimises support-related expenses and resources with a self-sufficient service. For example, this platform eliminates the need for password reset assistance – accounting for up to 60% of support desk inquiries, costing an estimated $15-70 per call – and customer validation. |
| MSSP services | 360-degree support
As an MSSP, we offer comprehensive end-to-end support for seamless evaluation, deployment, and ongoing assistance by:
|
| Technology | Minimal attack surface, no single point of failure
Our MFA solution employs advanced zero-knowledge proof of identity, ensuring a minimal trust surface and eliminating any single point of failure. Provides robust two-factor authentication, with the option of a software-only solution. |
| Data privacy | Zero information required
Our MFA solution does not require any Personally Identifiable Information (PII) from the end user. Instead, we only need a unique identifier, which may be a hash of a mobile number, email address, or username, thereby ensuring the solution’s adaptability to various identity schemes. |
The iGaming and online betting industry is constantly evolving, with new technologies and threats emerging regularly. Multi-factor authentication is an essential component of future-proofing betting and gaming platforms against these evolving risks. By integrating advanced authentication methods, iGaming and online sports betting operators can stay ahead of cyber threats and continuously protect their systems and players’ data.
Continent 8 is committed to supporting businesses in the iGaming and online sports betting industry with their cybersecurity needs. Our team of experts works closely with you to design and implement tailored MFA solutions that align with your regulatory requirements and business objectives.
To learn more about Continent 8’s MFA solution, contact Luana at luana.monje@continent8.com.
Craig Lusher from our Secure team provides a comprehensive analysis of the latest Distributed Denial of Service (DDoS) statistics from the first quarter of the year and their implications for cybersecurity trends.
The first quarter of 2025 has revealed significant changes in the DDoS threat landscape, characterised by a substantial increase in attack frequency, the emergence of ‘carpet bombing’ techniques and growing trends targeting the iGaming sector. With attack methodologies evolving and becoming more sophisticated, this report provides critical insights for cybersecurity planning and threat mitigation.
The first quarter of 2025 has shown a noticeable increase in DDoS attack activity, with 161 attacks recorded. This represents a rise from 4Q 2024’s 138 attacks and a dramatic increase from 1Q 2024’s 58 attacks. The most active month was February, which continues to show vulnerability during winter months.
1Q 2025 showed the following patterns in attack intensity:
While individual attack sizes appear smaller compared to historical peaks (2Q 2023’s 560.6 Gbps), this represents a strategic shift rather than reduced threat capability. Intelligence indicates that attackers now possess capabilities exceeding 500 Gbps but are employing more targeted and distributed approaches that can bypass traditional detection mechanisms.
1Q 2025 has shown a marked increase in attacks specifically targeting the online gambling and casino sector, with intelligence indicating a 400% rise in attacks against these entities since February. This industry-specific targeting represents a prominent trend that requires specialised attention and defence mechanisms.
Key statistics for 1Q 2025:
On 26 February, a carpet-bombing incident targeted 53 networks within a short 6-minute window (03:41-03:47 UTC). While this attack peaked at 150 Gbps with 120 Mpps, its distributed nature allows it to circumvent traditional defence systems, potentially resulting in a significant customer impact.
Comparing 1Q 2025 with recent quarters reveals several trends:
This shows a clear trend of increasing attack volumes over the past three quarters, with a 372% increase from 3Q 2024 to 1Q 2025.
While individual attack volume metrics appear to show decreasing intensity, this is misleading as attacks are now distributed across multiple targets simultaneously, making traditional detection mechanisms less effective.
The number of affected customers has increased dramatically in 1Q 2025, indicating a broader targeting strategy. Of particular note is the observed ‘spray’ technique that targets entire network Classless Inter-Domain Routing (CIDR) blocks rather than individual IPs, affecting multiple customers simultaneously.
1Q 2025 has seen the emergence of carpet bombing or spray attacks that distribute traffic across multiple hosts within targeted IP ranges. These attacks:
Comparing 1Q 2025 to 1Q 2024 shows significant changes in the threat landscape:
Intelligence indicates a notable correlation between DDoS attacks and subsequent data breaches in the iGaming sector. 1Q 2025 has seen examples of multiple organisations experiencing what appears to be a new attack pattern:
Unlike traditional ransomware operations, these attacks show no ransom demands prior to data release, indicating a potential shift in threat actor motivations from financial gain to maximum disruption or competitive advantage.
The transition to carpet-bombing techniques represents a significant evolution in DDoS tactics. These attacks distribute traffic across multiple targets within a network range, using traffic volumes per target that stay below conventional detection thresholds.
Intelligence indicates a targeted campaign against the iGaming sector, with a 400% increase in attacks since February 2025.
The average attack duration has increased dramatically to 4.3 hours, with the longest attack lasting 54 hours. Short, intense attacks (3-6 minutes) are now frequently observed as reconnaissance to test defence capabilities before launching larger campaigns.
Intelligence suggests a rising trend of AI technology adoption by threat actors. Self-hosted AI tools are enabling more sophisticated and unpredictable attack patterns that traditional defence mechanisms struggle to detect. These AI-enhanced attacks show several characteristics:
Based on 1Q 2025 attack patterns, particularly the emergence of carpet-bombing techniques, the following defence strategies are recommended:
The increase in attack volumes and sophistication in 1Q 2025 indicates a significant evolution in the threat landscape. Organisations should prepare for:
The 26 February incident, which affected 53 networks within a 6-minute window, demonstrates the effectiveness of these new attack methodologies and highlights the need for enhanced detection and mitigation capabilities.
Our best-in-class DDoS solution continues to evolve and in recent months we have amplified our scrubbing capacity to 5+ Tbps, as well as increased our scrubbing centres geographically deployed across multiple continents. Locations include Los Angeles, Chicago, New York, Miami, London, Amsterdam, Frankfurt, Singapore, Hong Kong and Sao Paulo.
Key features of our mitigation solution:
DDoS protection should also form part of a wider, multi-layered approach to cybersecurity. A 360-degree, end-to-end protection strategy should include DDoS mitigation solution as well as WAF/WAAP protection, MDR/EDR services, SIEM and SOC resources, VAPT assessments, backup solutions, and mobile device, phishing defence and MFA services.
This is the only way to have multiple protections in place for each attack type and to ensure the greatest level of resilience.
To learn more about how Continent 8 can help protect your organisation, contact a member of the team via sales@continent8.com or our Contact Us form.
The iGaming and online sports betting industry is facing unprecedented cybersecurity challenges, and multi-factor authentication (MFA) is becoming a crucial element for compliance and protection against cyber threats.

In this blog, Justin Cosnett, Chief Product Officer at Continent 8, will explore the cybersecurity landscape within iGaming, analyse the regulatory requirements for MFA in the US, discuss strategies for effectively navigating compliance while enhancing user experience and illustrate how passwordless MFA can be a game-changer in the iGaming industry.
In the rapidly expanding world of iGaming and online sports betting, cybersecurity has become a non-negotiable priority. As digital platforms proliferate, so do the threats aimed at them. Cyber criminals are constantly evolving their tactics, making it essential for operators to stay ahead of the curve. The stakes are high: a single breach can result in massive financial losses, reputational damage and erosion of customer trust.
Moreover, the nature of our industry, which involves real-time transactions and sensitive personal data, makes it an attractive target for cyber attacks. Implementing robust cybersecurity measures, including MFA, is not just about compliance; it’s about safeguarding the integrity of the gaming experience and protecting both the business and its players.
In the US, regulatory requirements for MFA vary by state.
Several regulated states have recognised the critical need for enhanced cybersecurity measures and have mandated the use of MFA for online gambling platforms. States such as Michigan, New Jersey and Pennsylvania are leading the charge – with others following suit – requiring operators to implement MFA to comply with state regulations.
These regulations are designed to protect consumers and ensure the integrity of the gaming environment. By requiring MFA, these states – and markets such as Brazil and Italy – aim to reduce the risk of unauthorised access and fraud, thereby fostering a safer and more trustworthy industry. Operators must stay informed about the regulatory landscape and ensure they meet all necessary requirements to avoid penalties and maintain their operating licenses.
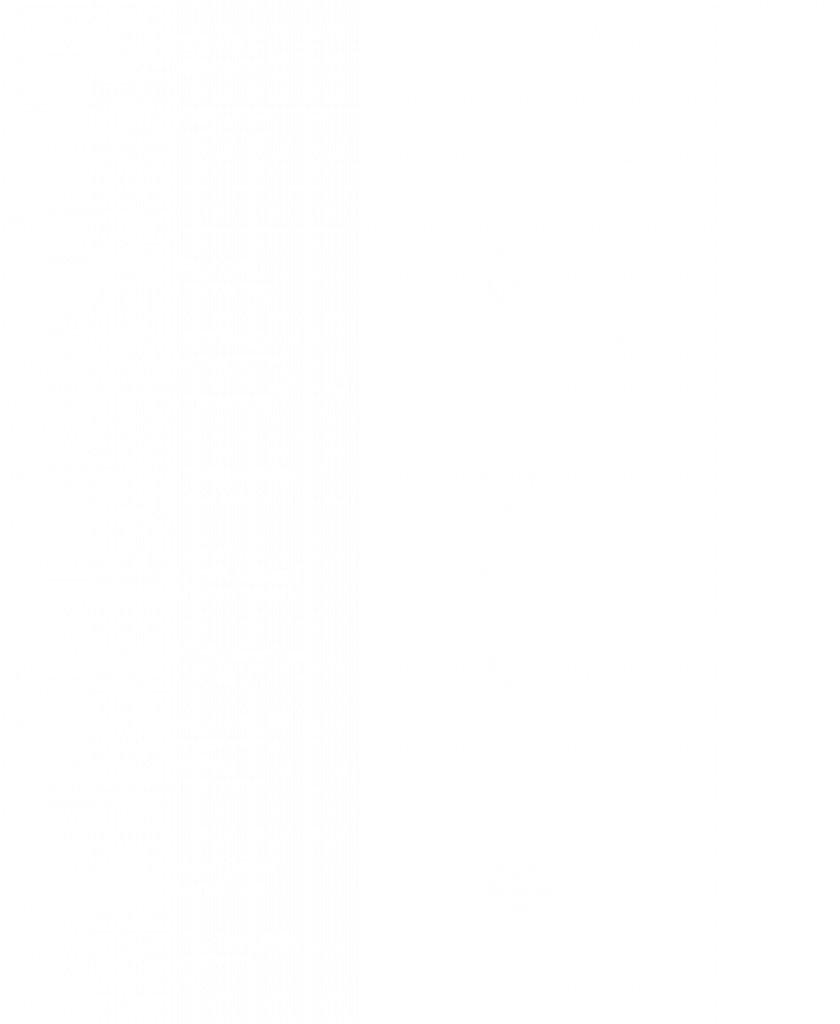
Implementing MFA comes with its own set of challenges, particularly in balancing compliance with user experience. No operator wants to add friction to the login process, especially given the rise of live betting on mobile apps.
Statistics show that 20-30%* of users abandon login attempts due to friction caused by complex authentication processes. For iGaming and online sports betting operators, this can translate in a decrease in player engagement and potential profit losses of up to 20%*.
Businesses must navigate the tightrope of stringent regulatory compliance while ensuring a seamless and enjoyable user experience. This often involves investing in advanced MFA solutions that offer robust security without compromising on convenience.
Continent 8, in partnership with MIRACL, offers a cutting-edge passwordless MFA solution that addresses both security and user experience challenges. MIRACL’s technology eliminates the need for traditional passwords, replacing them with a single-step authentication process that is both secure and user-friendly.
Key statistics underscore the effectiveness of this solution: a 99.9% reduction in account takeovers, a 70% decrease in user login friction and a significant increase in user satisfaction and retention rates. By leveraging MIRACL’s passwordless authentication, operators can provide a seamless and secure login experience that meets regulatory requirements and enhances customer loyalty.
Quick. Easy. Successful.
Continent 8 is committed to supporting businesses in the iGaming and online sports betting industry with their cybersecurity needs. Our team of experts works closely with customers to design and implement a tailored MFA solution that align with regulatory requirements and business objectives.
Trust Continent 8 to be your partner in navigating the complexities of cybersecurity and regulatory compliance in the gambling industry.
Are you compliant? Are you losing players at login? Are you missing out on revenue? See a live demo of our MFA solution on our rapid-fire webinar, ‘Passwordless MFA:
Improve player login and maximise profit potential’ hosted by Justin on Monday 10 March. Register here.
Craig Lusher from our Secure team provides a comprehensive analysis of the latest Distributed Denial of Service (DDoS) statistics from the fourth quarter of the year and their implications for cybersecurity trends.
The fourth quarter of 2024 marked a significant shift in DDoS attack patterns, with 138 recorded incidents. This represents a substantial increase from 3Q’s 37 attacks, though remaining well below historical peaks like 2Q 2023’s 1,106 attacks. October emerged as the most active month, aligning with historical patterns of increased 4Q activity.
This is a trend not just at Continent 8. In fact, 4Q also happened to see the largest DDoS attack ever recorded, with Cloudflare mitigating a 5.6 (Terabits per second) Tbps Mirai-variant botnet attack on one of their customers on October 29.
4Q 2024 demonstrated interesting patterns in attack intensity:
This quarter’s largest attack of 13.4 Gbps represents a decrease from 3Q 2024’s peak of 37.0 Gbps. For perspective, this is dramatically lower than 4Q 2023’s peak of 412.9 Gbps, indicating a significant shift in attack methodologies.
Key statistics for 4Q 2024:
Key statistics for 4Q 2024:
Comparing 4Q 2024 with recent quarters reveals several interesting trends:
This shows a significant escalation in attack frequency during 4Q.
While attack frequency increased, intensity continued to decrease throughout the year.
The decrease in affected customers coupled with the dramatic increase in attacks per customer suggests a shift toward more targeted campaigns.
Comparing 4Q 2024 to 4Q 2023 shows significant changes in the threat landscape:
The higher volume but lower intensity of attacks suggests a fundamental shift in attacker strategies, focusing on persistent, lower-threshold campaigns rather than high-impact events.
The concentration of attacks on fewer customers, with more attacks per target, indicates a move toward more sophisticated, focused operations.
The shorter average attack duration (17.6 minutes) combined with increased frequency suggests a tactical shift toward ‘pulse’ style attacks rather than sustained campaigns.
While individual attack intensities have decreased significantly year-over-year, the dramatic increase in frequency and focus on specific targets suggests an evolution in threat actors’ strategies. The pattern of increased 4Q activity appears to be holding true, though manifesting differently than in previous years.
Organisations should prepare for:
Our best-in-class DDoS solution continues to evolve and in recent months we have amplified our scrubbing capacity to 5+ Tbps, as well as increased our scrubbing centres geographically deployed across multiple continents. Locations include Los Angeles, Chicago, New York, Miami, London, Amsterdam, Frankfurt, Singapore, Hong Kong and Sao Paulo.
Key features of our mitigation solution:
DDoS protection should also form part of a wider, multi-layered approach to cybersecurity. A 360-degree, end-to-end protection strategy should include DDoS mitigation solution as well as WAF/WAAP protection, MDR/EDR services, SIEM and SOC resources, VAPT assessments, backup solutions, and mobile device, phishing defence and MFA services.
This is the only way to have multiple protections in place for each attack type and to ensure the greatest level of resilience.
To learn more about how Continent 8 can help protect your organisation, contact a member of the team via sales@continent8.com or our Contact Us form.
Jerad Swimmer, Regional Sales Director at Continent 8 Technologies, explores the benefits of Vulnerability Assessment and Penetration Testing (VAPT).

Tribal casinos are experiencing substantial financial growth. As highlighted in my previous blog, 2023 was a landmark year for the tribal gaming sector, with revenues hitting a record $41.9 billion USD, as reported by the National Indian Gaming Commission. Consequently, tribal casinos are increasingly targeted by cybercriminals, with reports suggesting a nearly 60% increase in cyber attacks on tribes in 2023.
With significant financial and personal data at stake, cybersecurity in tribal gaming and casino environments is a critical priority. But where should you start? In this blog, I’ll explain why Vulnerability Assessment and Penetration Testing (VAPT) is the perfect first step to bolster tribal gaming cybersecurity.
Let’s begin by defining VAPT. Craig Lusher, our Product Principal of Secure Solutions, describes VAPT as the following:
“VAPT is defined as a comprehensive set of cybersecurity services that helps organizations identify, assess and mitigate vulnerabilities in their IT infrastructure, applications and networks. Periodic Vulnerability Assessments (VAs) scan to detect exploitable vulnerabilities in customer networks and infrastructure and record them in a register, prioritizing remedial work and demonstrating continuous improvement. Penetration Tests (PTs) use identified vulnerabilities to further exploit and gain access, testing the efficacy of preventative security measures, procedures and technology.”
By simulating real-world cyber attacks, pentesting enables tribal casino IT and cybersecurity teams to identify system weaknesses and address potential vulnerabilities before they can be exploited by malicious actors. This strategy not only strengthens the casino environment but also ensures that cybersecurity measures remain robust and adaptable to evolving threats.
VAPT aims to establish what we at Continent 8 call a “hardened cybersecurity posture.”
A hardened cybersecurity posture integrates multiple protective layers, adhering to best practices for adaptability to threats and changes. It begins with technical controls such as network segmentation, access management and encryption, complemented by active defenses including web application and API protection, intrusion detection and cybersecurity monitoring. This approach is guided by policies and procedures for incident response and risk management.
The core components of a hardened cybersecurity posture create a robust defense system. Technical controls prevent attacks, while monitoring systems identify threats. Regular assessments are conducted to uncover vulnerabilities and governance ensures consistent implementation. This comprehensive approach ensures that even if one safeguard fails, multiple other layers remain to protect assets.
Implementing VAPT protocols is a beneficial practice for any tribal gaming organization. These measures not only bolster cybersecurity but also streamline internal and external audits.
By maintaining detailed records of testing and remediation efforts, casinos can demonstrate their commitment to cybersecurity to auditors. This transparency not only aids in passing audits but also enhances the casino’s reputation as a reliable and secure establishment.
Regular penetration testing provides tribal casinos with ongoing monitoring and enhancement of cybersecurity protocols, helping them stay ahead of potential cyber threats. This ensures a safer and more secure environment for both operations and players, while also building trust with internal and external parties and stakeholders. This proactive approach, again, is vital in preserving the casino’s integrity and reputation.
When choosing penetration testing tools for tribal casino and gaming cybersecurity, select tools that offer comprehensive coverage, capable of evaluating a wide range of vulnerabilities across multiple systems and applications.
A comprehensive VAPT service should encompass the following:
For more information on VAPT or to book a meeting with me at TribalHub Cybersecurity Summit or the Indian Game Tradeshow (Booth 18), contact me at jerad.swimmer@continent8.com.
Continent 8 provides comprehensive, multi-layered threat prevention, detection and response solutions to secure your tribal organization’s digital assets in the face of evolving cyber threats. For more information on how Continent 8 can support your cybersecurity initiatives, email sales@continent.com or fill out our Contact Us page.
Also, be sure to watch the latest episode in our Tribal Talks: Cybersecurity Unlocked podcast series – also available on Spotify – to gain a deeper understanding of the technological advancements, cybersecurity challenges and best practices shaping tribal gaming landscape.