
In the latest episode of Continent 8’s Ask the Expert podcast series, Craig Lusher, Principal Solutions Architect, sits down with Elizabeth Grima, Senior Executive Manager at New Dawn Risk, to unravel one of the most misunderstood – but increasingly critical – areas of iGaming resilience: cyber insurance.

Both experts have spent years helping operators navigate real-world incidents that strike without warning – from ransomware to payment fraud, account takeovers, and vendor outages. Their message is clear: cyber insurance is no longer optional – it’s a core component of operational continuity for any iGaming business.
If you haven’t had time to watch the podcast episode, below is a summary of the episode’s key takeaways.
The iGaming sector is one of the most attractive global targets for cybercriminals. High‑value financial transactions, player data, round‑the‑clock uptime requirements, and interconnected vendor ecosystems create a perfect storm of cyber risk.
Cyber insurance helps operators withstand these threats by providing a financial safety net – but also much more. Modern policies include:
This combination ensures operators can recover faster, smarter, and with less long‑term damage.
When a breach or outage occurs, every minute matters – and every minute is costly. Cyber insurance helps operators rapidly mobilise the right resources by covering:
This dual support – financial and operational – means operators can focus on restoring service and protecting players, rather than scrambling to fund or coordinate a crisis response.
A persistent misconception in the industry is that strong cybersecurity reduces the need for insurance – or vice versa.
In reality, the two work hand in hand:
Insurers increasingly expect baseline controls before offering coverage, including MFA, backups, monitoring, and social‑engineering safeguards.
Businesses that demonstrate strong cyber maturity often receive better pricing, fewer exclusions, and higher coverage limits.
Not all losses are automatically covered. Operators must pay close attention to key policy conditions:
Ensuring internal teams understand these requirements is essential for maximising protection.
Craig and Elizabeth highlight several myths that continue to cloud decision‑making across the industry:
Consider two of the most common (and costly) incidents:
An operator suffers a sustained DDoS attack during a major sporting event. Impacts include:
With cyber insurance, expert teams rapidly intervene, reduce downtime, and help restore services – while the insurer covers response and recovery costs.
When sensitive player data is exposed, expenses skyrocket:
Cyber insurance helps manage the fallout and protects the operator’s reputation.
To address the growing needs of iGaming operators, Continent 8 and New Dawn Risk have partnered to deliver a unified, industry‑specific cyber defence and insurance solution.
The partnership offers:
By combining Continent 8’s multi‑layered cyber protection with New Dawn Risk’s specialist insurance expertise, operators gain a comprehensive solution designed specifically for their operational and regulatory environment.
In an industry where downtime directly translates into lost revenue – and lost trust – cyber insurance has become a fundamental layer of resilience.
By integrating:
… iGaming operators can withstand today’s evolving threats with confidence.
The Continent 8 and New Dawn Risk partnership ensures that operators are not only protected – but empowered – to operate securely across multiple jurisdictions.
Watch episode 7 of Continent 8’s Ask The Expert podcast featuring New Dawn Risk
Cybersecurity regulation in Europe is evolving rapidly, and iGaming businesses must prepare now for two major incoming frameworks: the NIS2 Directive and the EU cyber resilience act (CRA). These regulations introduce stricter security obligations, tighter reporting deadlines and heightened accountability across the iGaming ecosystem.

In our recent webinar, “iGaming’s new cybersecurity rules”, Oliver Crofton (Regional Sales Director – Cybersecurity at Continent 8 Technologies) hosted an in‑depth discussion with Craig Lusher (Principal Solutions Architect EMEA at Continent 8 Technologies) and Jo Joyce (Partner and Head of Regulatory, IP & Digital at Taylor Wessing Ireland). Together, they provided clarity on the regulatory landscape and outlined what operators, suppliers and technology partners must do to stay ahead.
Here’s a breakdown of the key takeaways.
The iGaming industry operates in a high‑risk digital environment. Real-time financial transactions, complex technology stacks, and large volumes of sensitive personal data (including government-issued identity documents attached to financial information) make it a prime target for attackers. As cyber threats grow more sophisticated, regulators are raising the bar to ensure resilience.
NIS2 and the CRA aim to:
For iGaming, where uptime, trust and compliance underpin commercial success, these changes are significant.
NIS2 is fully live and enforcement has begun. This is no longer about preparation; the question is whether your organisation is compliant right now.
According to Craig and Jo, NIS2 represents a major overhaul of Europe’s cybersecurity framework. It replaces the original NIS Directive (2016), which was fragmented, voluntary in practice, and allowed each country to implement it differently.
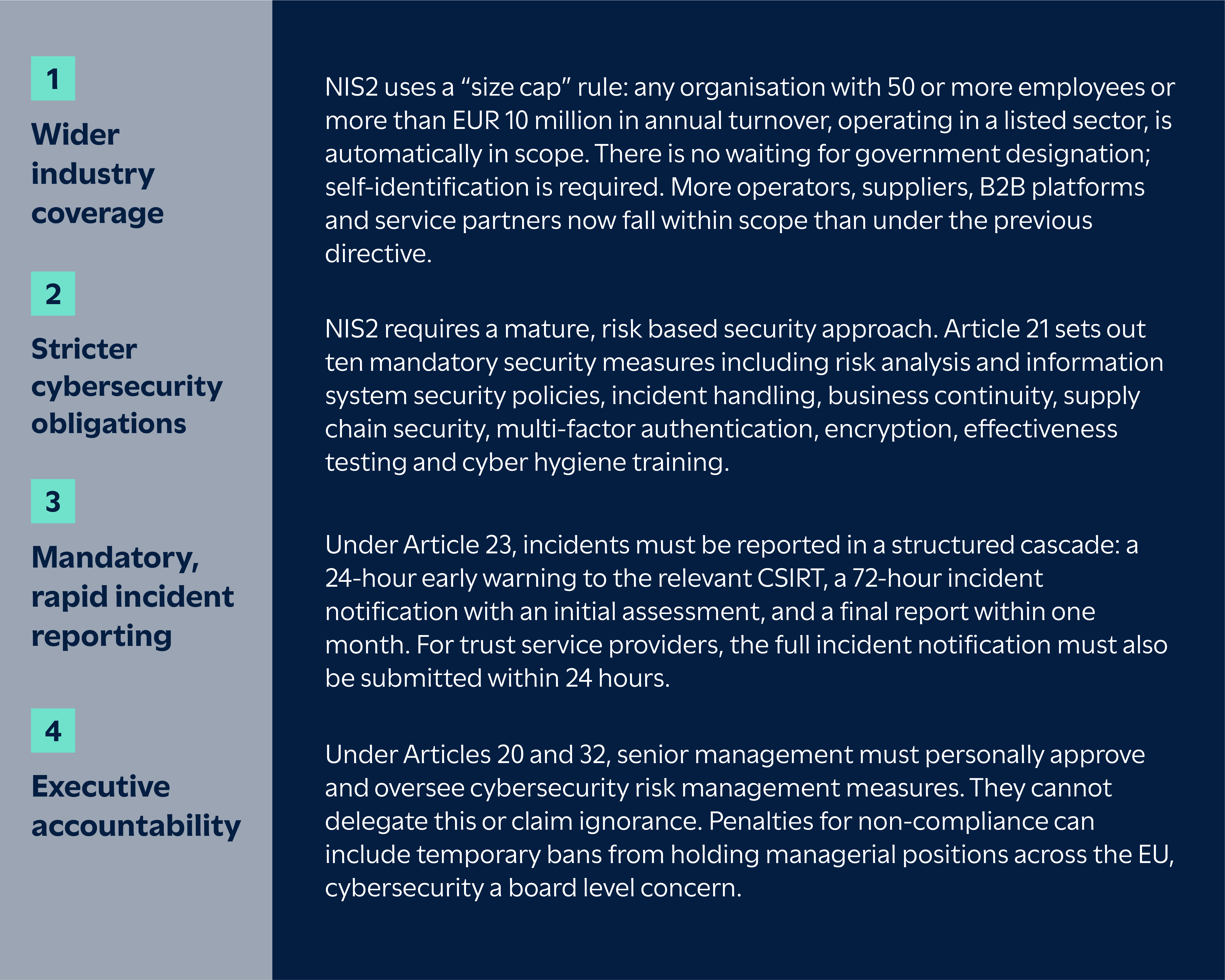
Key updates include:
Whilst NIS2 focuses on how organisations manage security, the CRA concentrates on the digital products those organisations depend on and produce.
CRA reporting obligations begin on 11 September 2026. From that date, manufacturers must report actively exploited vulnerabilities and severe incidents affecting the security of their products, following the same 24-hour early warning, 72-hour notification structure. For vulnerabilities, the final report must be submitted within 14 days of a corrective measure becoming available. Full product standards, including CE-marking requirements for software and connected devices, come into force in December 2027.

Jo highlighted that the CRA requires manufacturers and developers of digital tools – including gaming software, APIs, hardware and integrated systems – to
Given the heavy reliance on third‑party tech in iGaming, this places strong emphasis on vendor due diligence and supply‑chain oversight.
Jo: “I think one of the things that I’ve spotted is quite a lot of operators and firms within the iGaming ecosystem haven’t really necessarily accepted that they’re in scope.”
If your organisation provides or supports any of the following, NIS2 likely applies:
There are two additional points worth flagging. First, white-label and B2B providers are often managed service providers (MSPs) without realising it. If you run a player account management (PAM) system for 20 other brands, you are managing their core services, which, by definition, makes you an MSP. Under NIS2, MSPs are designated as essential entities, meaning they face ex ante supervision (proactive inspections and audits at any time), the same regulatory tier as a data centre or cloud provider.
Second, there is no “group privilege” under NIS2. If an internal IT arm provides services to the wider corporate group, it may be classified independently as an essential entity in its own right. Being part of a larger group does not shield individual subsidiaries or divisions from independent classification.
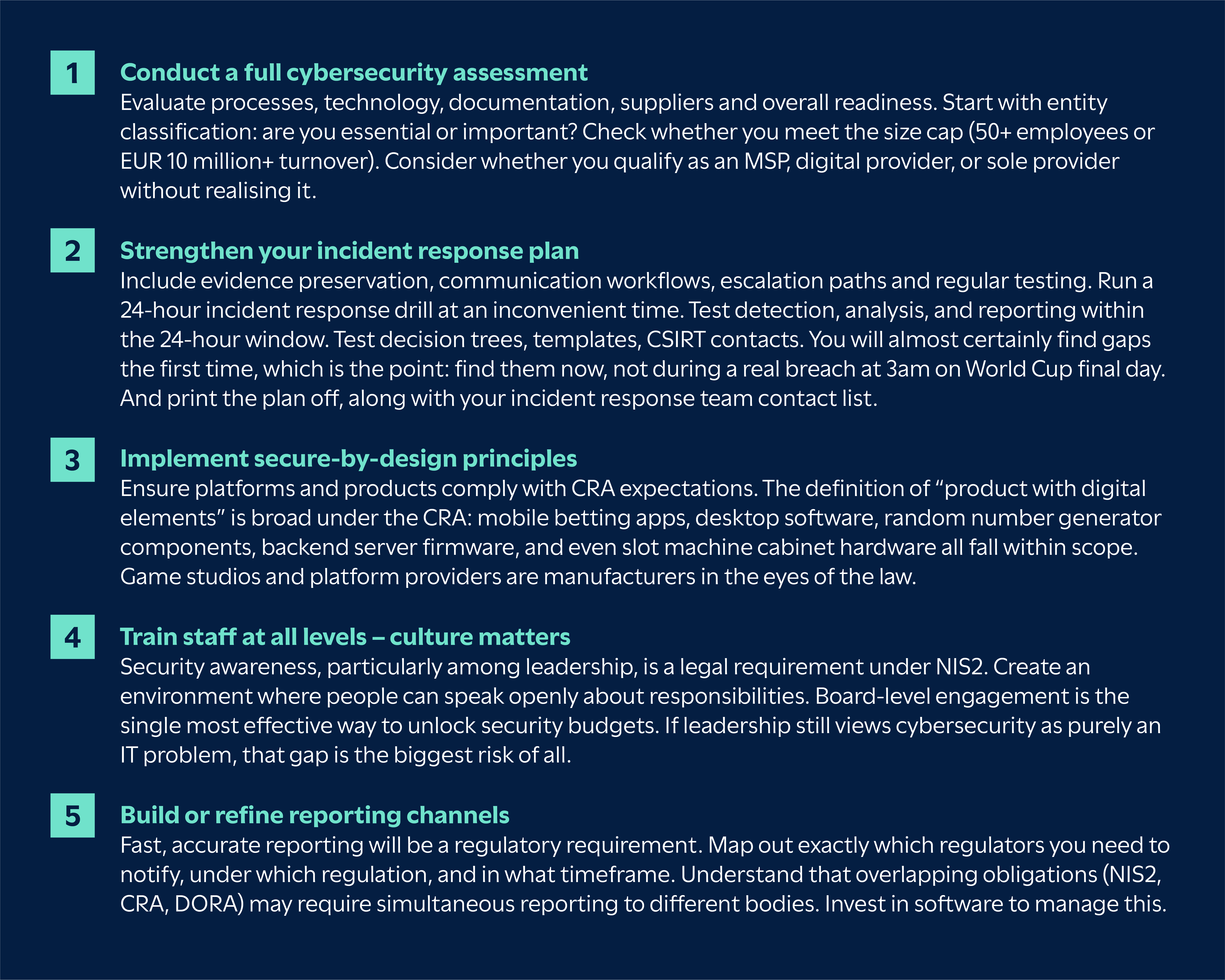
A readiness assessment is the essential first step.
Craig emphasised how the threat landscape facing iGaming businesses has intensified – including a 400% surge in cyber attacks targeting the gambling industry. This is not a gradual trend; attackers have industrialised their approach.

Operators and suppliers now face:
The interconnected nature of the sector amplifies the impact of any single vulnerability.
The cost of downtime in the industry now exceeds $6,000 per minute, and attacks are more visible in the news than ever, and recent breaches have seen hundreds of thousands of user profiles and identity documents exposed through relatively basic misconfigurations.
Craig highlighted several country‑specific differences in how NIS2 is being implemented, here are a few examples:
Malta moved faster than most EU member states, issuing Legal Notice 71 of 2025, with the CIPD as the ‘competent authority’. Self‑registration was due September 2025, so organisations that missed the deadline are now operating in a regulatory grey area. Governance and risk‑management controls must be live by March 2026, which at the time of the webinar was just weeks away.
Malta also goes further than EU baseline requirements by mandating a 24/7 security operations centre for digital infrastructure providers. Properly staffing a round-the-clock SOC requires at least 12 people to maintain a true rotation, which is a substantial operational investment for mid-sized operators.
The ultimate sanction isn’t just a fine; Malta can suspended MGA licences. For Malta-licensed gaming companies, this is an existential threat. If you lose your MGA licence, you are effectively locked out of dozens of global markets overnight.
Germany passed its implementation late, in November 2025. Registration deadlines for German‑based entities land in April 2026, leaving limited time for compliance.
Other member states are at various stages of transposition, and several missed the original October 2024 deadline. For operators with a presence in multiple EU countries, the practical challenge is managing compliance against several different national timelines and requirements simultaneously.
NIS2 is an EU directive, which means each member state must transpose it into national law. The result is that implementation timelines and specific requirements vary from country to country, and organisations operating across multiple jurisdictions need to track each one independently.
Both speakers stressed that NIS2 and the CRA require visible, ongoing engagement from senior management. Leading organisations will:
Under NIS2, leadership accountability is explicit. Executive training is not optional; it is a legal requirement under the directive.
Jo: “Just because something bad has happened doesn’t mean that you’re necessarily at fault… but you are going to have to produce reasonable reporting in layman’s terms… and explain that we’re operating in different risk parameters.”
Craig added the importance of training: “It’s mandatory for board‑level staff… you’ve got to keep training and constant training.”
Craig and Jo discussed the importance of reporting – especially when something goes wrong.
Jo: “The kind of reporting that one has to do under NIS2 is not a million miles away from the pre‑existing reporting… but there’s a real shift when you are experiencing a very serious incident.”
The 24‑hour reporting window is the operational flashpoint. Many companies are not ready for this. Under NIS2, the clock starts as soon as you become aware of a significant incident. You then have 24 hours to submit an early warning to the relevant CSIRT, 72 hours for a more detailed incident notification, and one month for the final report. A single incident can also trigger reporting obligations under the CRA and DORA simultaneously, each with different data requirements, formats, timelines and regulators.
Businesses need to prepare now by having supplier lists to hand, knowing exactly where to submit reports for each applicable regulation, and understanding that multi-jurisdictional reporting may be required.
Top tip from Jo:
Please print out a copy of your breach response plan… print out your incident response team list with phone numbers, ideally personal ones. If you can’t access your systems, it will take you an astonishing amount of time to pull this together.
Jo highlighted that enforcement activity under the CRA and NIS2 will be phased but increasingly serious.
From September 2026, the CRA introduces mandatory reporting of actively exploited vulnerabilities and severe incidents affecting product security. Full product‑related obligations take effect in December 2027, including the requirement for CE‑marking digital products, software included.
According to Jo, failure to report will likely be the first area where regulators take action, and penalties will be treated seriously.
Many NIS2 requirements are already enforceable. For essential entities that breach Articles 21 or 23, fines can reach up to EUR 10 million or 2% of total worldwide annual turnover, whichever is higher. For important entities, the maximum is EUR 7 million or 1.4% of worldwide turnover (Article 34 of NIS2). Regulators also have the power to issue binding instructions, order security audits, and, for essential entities, temporarily suspend or prohibit individuals from exercising managerial functions (Article 32(5)).
Jo: “They will factor in whether it’s going to bankrupt you… but they want these fines to hurt.”
This means businesses must act now to ensure reporting pathways, governance structures, supplier oversight and security controls are ready.
Craig and Jo recommended several clear actions for organisations:
There is a growing issue around the use of open‑source software (OSS) under the CRA. Although many OSS developers lobbied for exemption, OSS is widely used in commercial products. The CRA makes clear that organisations relying on OSS within regulated products remain fully responsible for meeting all cybersecurity and update obligations, including providing security updates for the minimum five-year support period.
Managing updates is difficult when you did not write the code – but the responsibility remains. The Software Bill of Materials (SBOM) requirement compounds this: manufacturers must maintain a machine-readable inventory of every library, open-source component and module in their products, kept as a living record.
Top tip from Jo:
If your business relies heavily on OSS, pay close attention to how it’s managed, seek specialist guidance and plan how you will meet long‑term update and security requirements.
The introduction of NIS2 and the EU cyber resilience act marks a significant shift for cybersecurity in iGaming. While the regulations bring real compliance challenges, they also create an opportunity for the industry to strengthen its defences, reduce operational risk and future‑proof operations.
Early preparation will help businesses stay compliant, competitive and trusted.
👉 Watch the full webinar here:
The 2026 Super Bowl weekend has once again demonstrated just how significant this event has become for the US sports betting ecosystem. This year’s matchup – New England Patriots vs. Seattle Seahawks at Levi’s Stadium – drew enormous national attention, with sportsbooks and operators preparing for yet another sharp spike in traffic and transaction volume. Super Bowl LX kicked off at 6:30 p.m. ET on February 8, with NBC broadcasting and Peacock streaming the game.
But what truly defined this year wasn’t just the on‑field drama – it was the scale and evolution of betting activity. Sportsbooks were expected to handle a record-breaking $1.76 billion in wagers across the US as betting continued to surge nationwide. Alongside traditional sportsbook action, prediction markets have been said to take center stage, allegedly boosted by a recent shift in federal regulatory posture. Industry analysts identified that, following a decision by the Commodity Futures Trading Commission to reverse its earlier proposal restricting political and sports-related contracts, platforms like Kalshi and Polymarket saw explosive participation heading into the game.
Notable betting storylines include a Nevada bettor who placed three preseason futures bets totalling $150,000 on Seattle – including $50,000 at 60‑1 odds for the Seahawks to win the Super Bowl – secured a combined payout approaching $4.5 million after Seattle’s championship win. These futures wagers represented some of the largest liabilities for US sportsbooks this season, highlighting the growing sophistication and long‑horizon strategies of certain bettors.
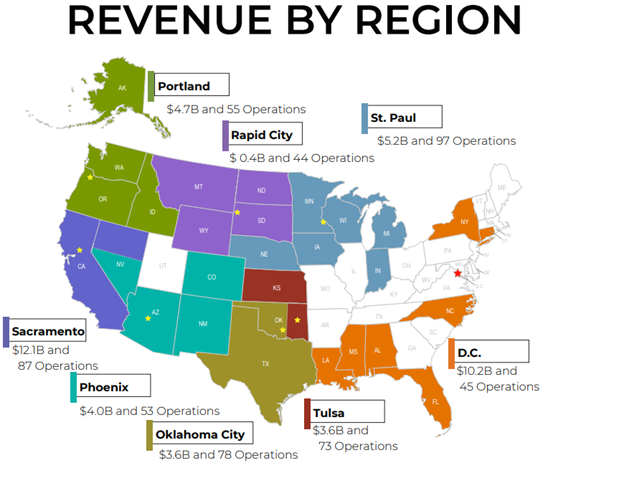
Our Super Bowl 2026 infrastructure performance reflected the scale and intensity of this year’s betting and iGaming activity. A review of Continent 8 network data revealed several notable trends across connectivity, cloud workloads, and B2B platform traffic:
Outbound traffic from transit customers to hyperscale cloud providers between Feb 9, 2026 (00:00) and Feb 10, 2026 (10:00)
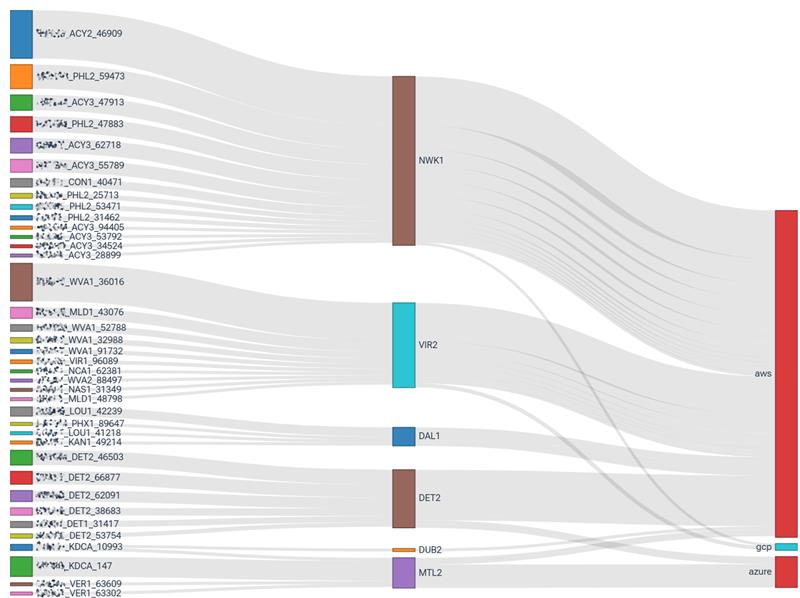
Outbound traffic from US transit customers to all destination ASNs from Feb 6, 2026 (00:00) to Feb 9, 2026 (10:00)
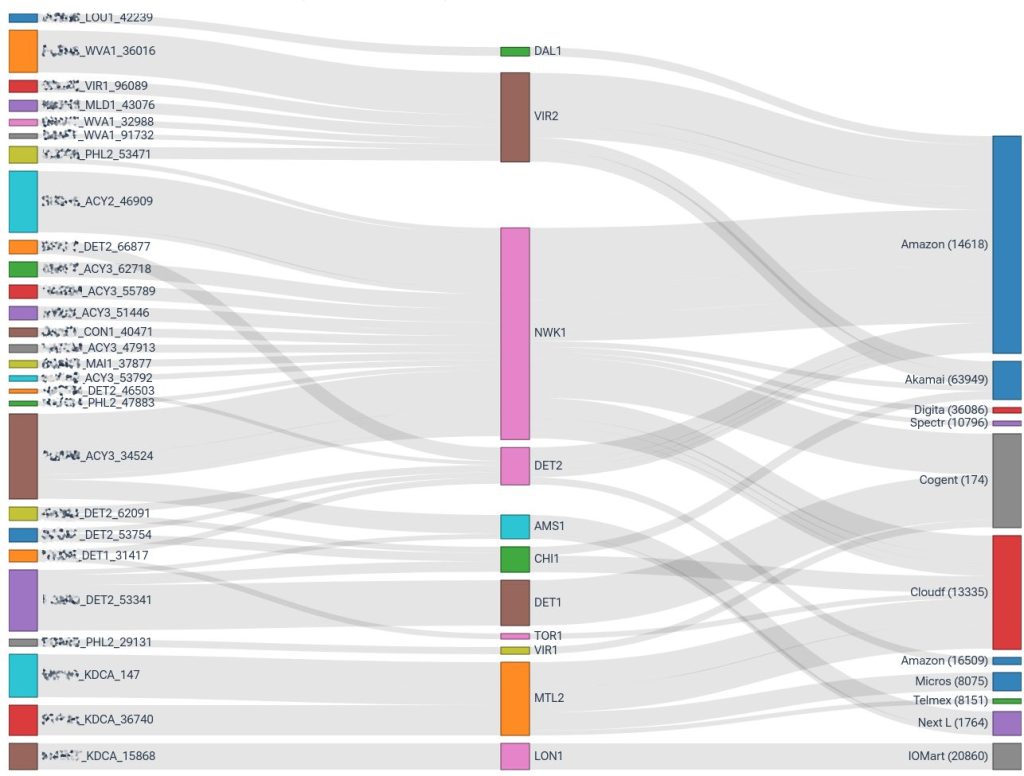
These insights highlight how operators, platforms, and cloud‑driven services collectively leaned on Continent 8’s global network to handle one of the busiest betting weekends of the year – ensuring fast, secure, and uninterrupted connectivity throughout Super Bowl week.
In the weeks leading up to any Super Bowl, the world sees the spectacle on the field – but behind the scenes, operators rely on robust, resilient infrastructure to support record-breaking engagement. For Continent 8, preparation for Super Bowl LX began months in advance, with teams across the business working to ensure a seamless and interruption‑free experience for customers.

Justin Cosnett, Chief Product Officer, explains the technical groundwork:
“Our technical preparation began months prior to the Super Bowl. This centred around infrastructure and network upgrades and optimisation – including bandwidth increases in all key peering and IX locations, cloud infrastructure refreshes, among other changes – to ensure an interruption‑free operation.”
As the big weekend approached, this preparation evolved into a detailed readiness programme built around five core pillars:
This disciplined, collaborative approach ensured that every layer of our infrastructure was optimized for the surge in demand.
While a Super Bowl broadcast lasts just over 3 hours and 37 minutes, our “live” operational window was far broader – spanning five continuous days, from Thursday through Monday. During this period, Continent 8 operated in full Super Bowl mode, with:
This extended readiness window allowed us to anticipate and respond to shifting traffic patterns as early Super Bowl wagering, promotional campaigns, and late‑week betting surges ramped up toward game time.
Continent 8 teams were monitoring network performance across our global ‘locker rooms,’ ensuring optimal conditions no matter where traffic originated.

Dublin Office

Montreal Office
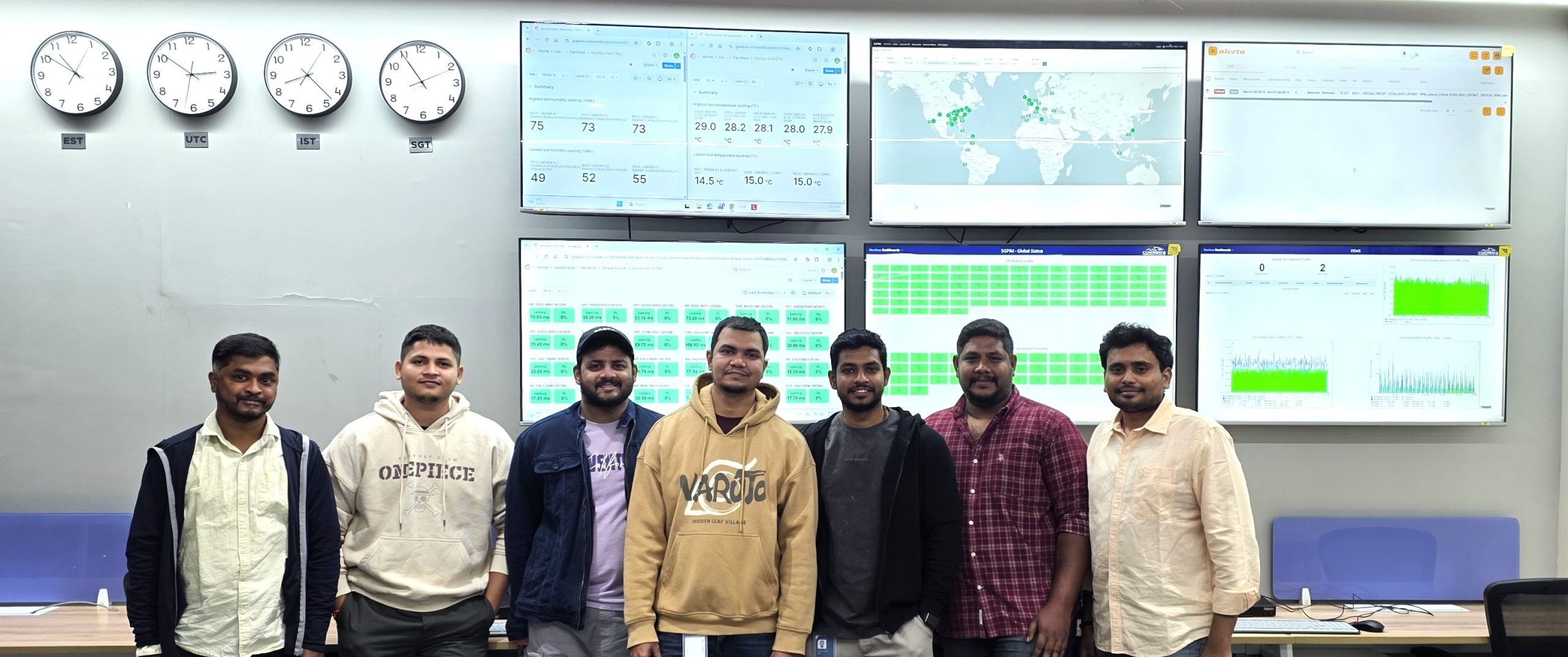
India Office
Long after the final whistle, our work continued. With operators still handling settlement workloads, futures reconciliations, and continued user engagement, network oversight remained critical.
Our Major Incident Management playbook provided structure and clarity throughout the Super Bowl cycle – guiding decision‑making, enabling cross‑team coordination, and serving as a framework for continuous improvement as we transition to subsequent peak events.
Reflecting on this year’s performance, Justin emphasised the impact of the team’s meticulous planning:
“The entire Continent 8 team was instrumental in ensuring a flawless Super Bowl experience. This careful, meticulous planning underscored our commitment to delivering a reliable and unparalleled service to our customers, allowing millions of players to place their bets and engage with the event in real-time.”
The Super Bowl remains the most demanding annual event for US sports betting operators – and 2026 raised the bar again. With sportsbooks handling unprecedented wagering volume and prediction markets adding an entirely new category of high-frequency transactions, operators faced rapid and unpredictable load spikes that required resilient, low-latency infrastructure.

As demonstrated by Super Bowl weekend 2026, operators need to prepare not just for higher traffic, but for traffic patterns that are more volatile, more complex, and more continuous. Ensuring uptime, security, and latency control during these surges is essential to delivering a fault‑free betting experience.
“Super Bowl weekend is one of the biggest moments of the year for our North American customers, and we take that responsibility incredibly seriously. Our team prepares months in advance to ensure operators experience flawless uptime, ultra‑low latency, and the resilience they need when traffic hits its peak. At Continent 8, going the extra mile isn’t the exception – it’s what we deliver every day, and especially during the industry’s biggest events.”
Aidan Rees‑Williams, Head of North America Sales, Continent 8 Technologies
As the US sports betting landscape accelerates – now fueled not only by sportsbook adoption but also possible regulatory green lights for prediction markets – operators require partners who can manage mission‑critical digital resilience at national scale.
Continent 8’s US presence is uniquely aligned to support this environment because we offer:
Contact our team to learn more.

In cybersecurity, intelligence is power. Financial institutions and healthcare providers have long relied on threat intelligence platforms to anticipate attacks and protect critical assets. Yet, the gambling industry, despite handling billions in transactions and sensitive customer data, has been slower to adopt this proactive approach.
The stakes are high. Cyber incidents targeting gaming operators have surged dramatically, with attacks becoming more sophisticated and financially devastating. We have seen land-based casinos forced offline for days.
For an industry built on trust and real-time engagement, the question is no longer whether operators need intelligence, but how quickly they can integrate it into their security posture.
Consider financial services. Banks operate under constant threat from fraud, phishing, and ransomware, yet they’ve built robust intelligence-sharing ecosystems like FS-ISAC (Financial Services Information Sharing and Analysis Center). These platforms allow members to share threat intelligence in real time, creating collective defence that benefits the entire sector.
Gaming needs its own equivalent, but with crucial differences. Our adversaries are unique: organised crime groups targeting high-roller accounts, bonus abuse rings operating across dozens of operators, match fixers probing betting platforms, and in certain jurisdictions, nation-state actors targeting offshore operations. Generic threat intelligence platforms miss approximately 70% of gaming-specific attack patterns because they weren’t designed to recognise these threats.
Effective threat intelligence transforms security operations across several critical areas.
Smarter vulnerability management:Gaming operators run complex technology stacks spanning payment processors, gaming engines, live betting platforms, and player databases. Patching everything according to generic severity scores is impossible during live operations. Intelligence changes the equation from “how severe could this be?” to “is this being actively exploited against gaming platforms now?” When intelligence reveals a payment gateway vulnerability under active exploitation against European operators, that patch moves to the front of the queue regardless of theoretical severity.
Faster incident response:Intelligence enables teams to build playbooks for gaming-specific scenarios before incidents occur. When attacks happen, context accelerates decisions. A generic PowerShell alert becomes high priority when intelligence identifies it as a technique used by gaming-targeting ransomware groups. The MITRE ATT&CK framework provides common language for this intelligence, allowing teams to measure defensive coverage objectively and identify gaps systematically.
Example: Champions League final, an operator detected unusual API calls to their odds calculation engine. Intelligence immediately revealed the same pattern had appeared at three other sportsbooks in the preceding 48 hours. A pre-built playbook isolated affected systems automatically. The attack was contained in four minutes rather than 45.
Proactive threat hunting:Shared intelligence generates hunting hypotheses no single operator could develop alone. When multiple operators detect reconnaissance against payment systems using specific techniques, everyone can search for identical indicators. Security teams shift from reactive firefighting to actively hunting for bonus abuse automation, payment fraud patterns, and early reconnaissance.
Reduced alert fatigue:Gaming platforms generate millions of security events daily. Intelligence-driven contextualisation transforms “this IP attempted 50 logins” into “this IP is part of a credential stuffing botnet that hit six gaming sites today.” Alerts receive priority based on actual gaming industry impact. Analysts escape false positive overload and focus on genuine threats.
Intelligence extends beyond traditional cybersecurity. iGaming’s ecosystem of platform providers, payment processors, and affiliate networks creates significant supply chain risk. When a major provider suffers a breach, operators need immediate notification and indicators to hunt for compromise in their own environments.
Fraud prevention benefits enormously from shared intelligence. Credential stuffing, bonus abuse rings, and synthetic identity creation operate across multiple operators simultaneously. Real-time sharing allows the entire industry to block known fraudsters before they cause widespread damage.
iGaming operates under intense regulatory scrutiny across multiple jurisdictions. Intelligence programmes must account for data sovereignty when sharing across borders, maintain evidence chains for incident reporting, and demonstrate due diligence to regulators.
Rather than complicating compliance, intelligence sharing strengthens it. Documented participation demonstrates proactive security investment. Standardised incident categorisation streamlines reporting. Cross-operator intelligence identifies systemic risks that regulators will certainly notice even if individual operators miss them.
None of this works without trust. Operators compete fiercely, and sharing incident details raises legitimate concerns about competitive exposure.
Effective programmes offer anonymity where needed – operators can share indicators without identifying themselves. Clear data governance establishes who accesses what information. Critically, the value must be obvious. Operators need to see that participation makes them measurably safer, that what they receive far exceeds what they contribute. As membership grows, network effects compound: more operators sharing means better intelligence for everyone.
Gaming operations run around the clock with no maintenance windows during major sporting events. Attacks deliberately target peak revenue periods. Response times measured in hours are unacceptable.
This demands SOAR (Security Orchestration, Automation & Response) automation. When intelligence identifies malicious infrastructure, indicators must flow automatically into firewalls and detection systems. Pre-configured playbooks must execute without waiting for human intervention.
Operators with mature programmes report mean time to detect dropping from 14 hours to under 10 minutes. Mean time to respond falls from four hours to 12 minutes. False positives reduce by 70%.
With average gaming breach costs exceeding $5M including regulatory fines and customer compensation, preventing one major incident justifies significant investment. When a zero-day in payment gateway software was identified through shared intelligence, operators with access isolated vulnerable systems 48 hours before public disclosure. Those without suffer breaches averaging $5M each.
The gaming industry has reached an inflection point. We can continue operating in silos, or recognise that collective defence serves everyone’s interests. The attackers are already collaborating; we must do the same.
Financial services learned this lesson years ago. For gaming, the question is whether we learn proactively or wait for a sector-wide incident to force the conversation.
For more information on Threat Exchange, visit continent8.comor email sales@continent8.com.
**Source: EGR Digital Edition 248
Artificial Intelligence (AI) is rapidly reshaping how governments, enterprises, and communities operate – and tribal nations are no exception. To explore these opportunities, the Tribal Leadership Council, in partnership with Continent 8 Technologies, recently hosted a specialised webinar titled “Practical AI for Tribal Organizations.”
The session featured two expert presenters:
These speakers guided attendees through a practical, sovereignty-focused understanding of how AI can support tribal governance, cybersecurity, community engagement, and enterprise operations.
It was important to Cris to set the scene on AI from the offset – and the fact that AI is not a single product or technology – it’s a broad set of capabilities that are already embedded in much of the systems and software we use today.
With that said, below is a summary of the key insights shared during the webinar.
AI is no longer a future concept – it is a tool tribal leaders can use right now to increase efficiency, strengthen decision-making, and improve the delivery of services. The webinar highlighted the ability of AI to:
By automating repetitive tasks and analysing information at scale, AI frees tribal leadership to focus on strategy, sovereignty, and community impact.
Cris stressed that the success of AI isn’t dependent on the algorithm, but the quality of the data used: “trash in, trash out.”
Jerad and Cris outlined a crucial distinction between generative AI and agentic AI – two categories that offer very different capabilities and also associated risks.
Designed to create content.
Useful for drafting policies, summarizing documents, producing reports, or generating communications. Content should always be verified – there is a risk for errors and hallucinations.
Designed to take actions based on rules or goals.
Capable of performing tasks such as compliance checks, initiating workflows, alerting staff, or managing routine operational processes.
Understanding the difference allows tribal organizations to choose the right AI tool for the right job – and avoid over-automating areas that require human oversight.
Key takeaway: generative AI assists people, whereas agentic AI acts on behalf of the organization.
Examples shared during the webinar demonstrated how AI can streamline workflows, including:
One powerful use case: automating regulatory certification steps reduced staff workload while improving accuracy – allowing tribal teams to focus on meaningful leadership and community priorities. One tribal organization took a 6-month manual process down to a 2.5-week workload.
AI-powered tools can enhance how tribes communicate with and support their citizens. This includes:
These capabilities help tribal governments stay connected to their people while reducing demand on staff.
But it’s important to understand: AI does not replace human judgment or community leadership.
The presenters also explored how tribal enterprises – from gaming to hospitality to broadband and beyond – can benefit from AI through:
These efficiencies translate to better productivity, fewer errors, cost savings, and stronger competitive advantage.
From data exposure and enhanced fraud, it is important tribal leaders understand the risks associated with AI. Sensitive data should be kept out of public platforms.
Both speakers emphasized that AI adoption must reinforce – not compromise – tribal sovereignty. Key considerations include:
These measures ensure tribal nations maintain full control over their data, decisions, and digital future.
As AI expands, cybersecurity must evolve with it. Cris highlighted essential protections such as:
AI itself can strengthen cyber defense by detecting suspicious activity earlier and accelerating response times.
The speakers outlined a practical roadmap for responsible, sovereignty-aligned AI implementation:
AI is not about replacing people or traditions. It is about protecting sovereignty, improving services, and controlling your digital future.
By taking a careful, strategic approach, tribal leaders can harness AI to strengthen governance, protect sovereignty, and uplift their communities.
You can watch the full webinar recording here:
In the iGaming industry, trust is everything – not just for players, but for the entire ecosystem of operators, suppliers, and technology providers. Players expect seamless experiences, secure transactions, and confidence that their personal data is protected. At the same time, suppliers and platform partners demand robust cybersecurity standards and transparent risk management to safeguard their own systems and reputations. Yet, as the sector grows – driven by new markets, mobile-first platforms, and real-time betting – the attack surface expands exponentially. Cybercriminals have noticed. From ransomware groups to phishing campaigns, the industry is now a prime target for sophisticated attacks that exploit both technology and human behaviour.

Recent analysis shows a 400% surge in cyber incidents impacting casino operators and gambling businesses since early 2025. The cost of downtime during a major sporting event can exceed $6,000 per minute, and phishing attacks have grown by 180% since 2023. These numbers underscore a stark reality: the iGaming ecosystem is under siege.
The past year has been a wake-up call for the industry. In July 2025, Flutter Entertainment, owner of Paddy Power and Betfair, confirmed a breach affecting up to 800,000 users, exposing personal data such as IP addresses and betting activity. In March, Merkur Group, a major European casino operator, suffered a catastrophic incident that compromised sensitive data across multiple platforms, including payment details, identity verification documents, and over 70,000 ID scans, all due to misconfigured backend interfaces. Beyond data theft, account takeover attacks surged by 42% in Q1 2025, with one European betting platform losing €1.7 million in just 48 hours before detection. These examples illustrate a clear trend: attackers are exploiting both technical vulnerabilities and human factors, and the financial and reputational stakes have never been higher.
Why is the industry a target? Because it offers two things that attackers value most – money and data. Every payment gateway, affiliate integration, and game studio aggregation introduces new vulnerabilities. Add to this the complexity of real-time transaction engines, regulatory reporting systems, and third-party content providers, and you have an environment where a single weak link can compromise the entire chain.
Now that I have set the scene, here’s what I believe will shape cybersecurity in iGaming in 2026.
Artificial Intelligence is the double-edged sword of cybersecurity. In 2026, expect AI-driven attacks – deepfakes, automated intrusions, and identity-centric exploits – to become mainstream.
On the defensive side, AI will power advanced threat hunting, anomaly detection, and predictive analytics. Operators will deploy machine learning models to identify fraudulent transactions in real time and detect behavioural anomalies before they escalate. But securing AI itself will be critical as attackers are already targeting AI systems to turn them into insider threats.
Cybersecurity will move from being a compliance checkbox to a strategic KPI. This is a welcome shift for the industry. Regulators are demanding real-time, machine-readable compliance data, while players increasingly view security as part of the user experience. Seamless onboarding, frictionless withdrawals, and transparent data handling will become loyalty drivers.
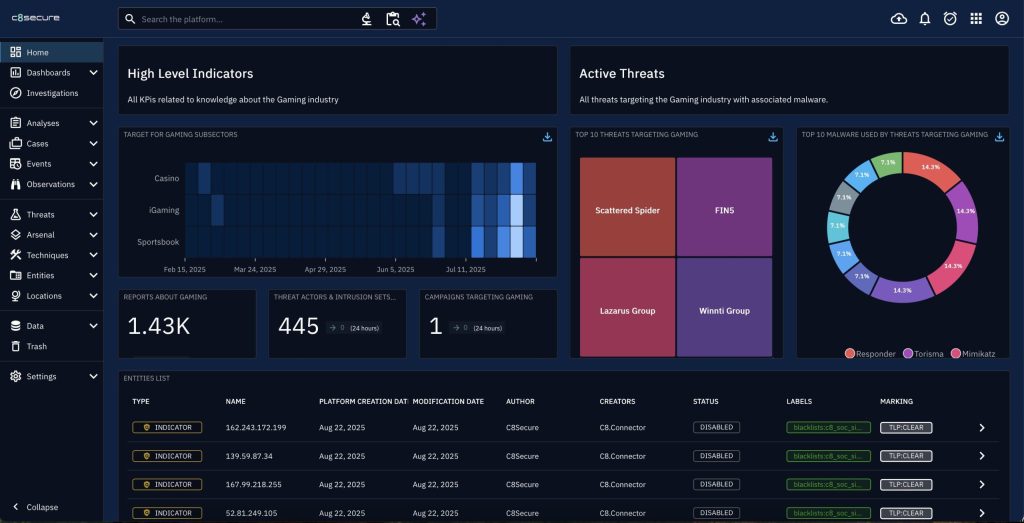
The complexity of today’s threat landscape means no single operator can fight alone. Intelligence sharing will become the cornerstone of industry-wide defence. This is where Continent 8’s Threat Exchange sets a new benchmark.
Launched in late 2025, Threat Exchange is the industry’s first dedicated cyber threat intelligence (CTI) platform, engineered specifically for iGaming and online sports betting. It processes billions of signals daily, delivering real-time, actionable insights to operators, platform providers, and regulators.
Key capabilities include:
As I often say, “Threat Exchange is changing the game.” By leveraging our position as the industry’s trusted cybersecurity and hosting partner, we transform vast datasets into clear, actionable intelligence. This isn’t just about detecting threats – it’s about anticipating them and enabling proactive resilience.
Jurisdictions from Brazil to Finland are introducing competitive licensing models, while established markets like the UK are tightening advertising and security requirements. Compliance will increasingly rely on API-driven automation, enabling operators to feed regulators real-time data on transactions, safer gambling measures, and incident response.
To thrive in this environment, operators should:
Cybersecurity in iGaming is no longer about reacting to incidents – it’s about anticipating them. Those who harness intelligence, embrace collaboration, and embed security into every layer of their operations will not only survive but lead.
For more information on how Continent 8 can support your initiatives, email sales@continent.com or fill out our Contact Us page.
As we approach the end of 2025, Justin Cosnett, Chief Product Officer, has been reflecting on what has been an extraordinary year for Continent 8 Technologies. Our mission to deliver secure, innovative, and customer-focused solutions has never been more important, and this year we’ve achieved milestones that truly set us apart. From expanding our global footprint to driving cutting-edge cloud and cybersecurity solutions, 2025 has been a year of recognition and success.

We were proud to be a double winner at the 2025 Baltic & Scandinavian Gaming Awards during the MARE BALTICUM Gaming & TECH Summit in Vilnius, Lithuania, taking home:
And that’s not all – Continent 8 was also named Data Centre and Cloud System Provider of the Year at the prestigious EGR B2B Awards, cementing our position as a trusted leader in the industry.
Here are eight standout moments that defined our journey in 2025.
Cybersecurity is at the heart of everything we do. This year, we launched the Continent 8 Threat Exchange, a collaborative platform that empowers customers to share threat intelligence and strengthen defences against evolving attacks. It’s a game-changer for proactive security.
As Patrick Gardner, our Chief Security Officer, said: “The Threat Exchange is a one-of-a-kind initiative for our industry. It gives customers the ability to collaborate and act on real-time intelligence, creating a stronger, united defence against cyber threats.”
In April, we hosted our annual Customer Advisory Board in Ireland, bringing together our trusted customers and partners. The event is designed to share insights and help shape the future of our services. These conversations are invaluable – they ensure we remain aligned with customer needs and market trends.
A proud moment for all of us was seeing our Founder and CEO, Michael Tobin, receive major industry recognition, ranking among the top global tech leaders in GamblingIQ’s Trusted 10 list. His vision and leadership continue to inspire our team and drive innovation across the business.
GamblingIQ’s commentary on Michael mentioned: “Michael Tobin has become one of the defining figures in iGaming infrastructure… In an industry often chasing the next big thing, Tobin embodies the kind of leadership that prioritises stability and sustainable growth without losing sight of innovation.”
We successfully migrated Sportingtech from a VMware-based environment to a Nutanix AHV hyperconverged infrastructure, delivering enhanced scalability, resilience, and compliance. This strategic move helped Sportingtech avoid a 42% increase in virtualisation costs following VMware licensing changes.
The cloud migration was no small feat:
Read the full case study here
Knowledge sharing is key to progress. This year, we launched the Ask The Expert podcast series, offering insights from specialists on topics like iGaming infrastructure, cybersecurity, cloud strategy, and compliance. We have welcomed guest speakers from AWS, Sportingtech and Nutanix. It’s become a valuable resource for the industry.
All the episodes can be viewed here
You can expect more episodes in 2026!
Our partnership with Alea went beyond technical collaboration – it became a platform for driving industry-wide awareness of the importance of cybersecurity for gaming. Alea, one of the fastest-growing iGaming aggregators, handles over 21,000 transactions per second and connects operators to 16,000+ games from 160 providers via a single API. Securing this scale of operations is critical, and together we’ve raised the bar for cybersecurity standards in the sector.
This collaboration was showcased at SBC Summit Lisbon, where we hosted a press conference to emphasise proactive security measures for operators and suppliers.
Security layers matter. We rolled out our MFA solution, adding an extra level of protection for customer environments and reinforcing our commitment to safeguarding critical systems. It also ensures regulatory compliance across iGaming jurisdictions and markets.
Continent 8’s one-step login solution, powered by MIRACL, has a proven success rate of 99.9%, taking on average just two seconds to login. It is also designed to reduce an organisation’s support costs.
We have recently signed a major US operator (more on that news soon!) and expect to announce some exciting partnerships in 2026.
We achieved ISO 50001 certification, demonstrating our dedication to energy efficiency and sustainability across our global data centre operations. This is an important step toward a greener future.
Michael Tobin said: “Achieving ISO 50001 certification is a significant step in our commitment to sustainability, and I’d like to congratulate all involved in this accomplishment. This certification ensures that our organisation is responsible for continuously enhancing our energy management system and implementing objective and best practices for energy efficiency.”
***
2025 has been a year of innovation, collaboration, and growth. I want to thank our customers, partners, and the incredible Continent 8 team for making these achievements possible. As we look ahead to 2026, we remain committed to delivering secure, resilient, and forward-thinking solutions for the industry.
Following the release of the National Indian Gaming Commission’s (NIGC) Fiscal Year (FY) 2024 Gross Gaming Revenue (GGR) report, Jerad Swimmer, Regional Sales Director at Continent 8 Technologies, provides a mid-year report on the state of tribal gaming in 2025.
On July 31, the NIGC published its annual GGR report, highlighting a record-setting $43.9 billion in revenue for FY 2024. This achievement reflects a 4.6% year-over-year increase, representing growth of $2 billion, with data collected from 532 gaming operations run by 243 federally recognized tribes across 29 states. In the NIGC press statement, Acting NIGC Chairwoman Sharon Avery remarked:
“This year’s GGR reflects not only the resilience of the tribal gaming industry, but also the dedication of tribal leadership in preserving and growing this important economic driver for their communities. The continued success of Indian gaming is a testament to the strong tribal governance and the sound regulation that protects the integrity of the industry.”
These figures emphasize the critical economic contribution of tribal gaming, supporting essential initiatives across employment, infrastructure, education and social services within tribal communities. Yet, as the tribal gaming industry’s financial impact continues to expand, so does its exposure to cyber threat actors aiming to benefit from this growth.
Over the past year, the industry has witnessed significant cyber incidents. In April of last year, a tribal casino was forced to suspend its operations following a cyber breach and advised patrons to monitor account activity for potential unauthorized access. In February of this year, one tribe experienced a ransomware attack that disrupted telecommunications and IT systems across multiple tribal entities, including casino operations.
During recent key industry events – including the OIGA Conference and Trade Show, the Indian Gaming Convention and Tradeshow (IGA) and the TribalHub Cybersecurity Summit – our team has also received direct reports of numerous cybersecurity incidents. These events have resulted in a range of financial, operational and reputational impacts for affected organizations. These forums have provided tribal casinos, gaming commissions and government bodies in Indian Country with valuable opportunities to share their cybersecurity challenges and engage with experts on effective threat mitigation strategies.

Given the ongoing and evolving cyber threat landscape, tribal gaming organizations must adopt a proactive cybersecurity posture – operating with an ‘assume breach’ mindset and prioritizing resilience. Robust measures are essential to safeguard infrastructure, player data, critical platforms and preserve tribal sovereignty. Recommended best practices for comprehensive cyber defense include:
As a trusted Managed Security Service Provider (MSSP), we partner with tribal gaming organizations – including Cherokee Tribal Gaming Commission (TGC), ShowNation, Tachi Palace Casino Resort – to foster a culture of cybersecurity awareness, strengthen organizational security posture and ensure long-term operational resiliency.
Continent 8 provides comprehensive, multi-layered threat prevention, detection and response solutions to secure your tribal organization’s digital assets in the face of evolving cyber threats. For more information on how Continent 8 can support your cybersecurity initiatives, email sales@continent.com or fill out our Contact Us page.
Also, be sure to listen back to our Tribal Talks: Cybersecurity Unlocked podcast series. Each episode delves into new stories, insights gained, best practices and key developments that are shaping the future of tribal casino gaming and cybersecurity.
Key highlights:
In the iGaming and online sports betting industry, where cybersecurity breaches can result in unauthorised access, identity theft, account takeovers, operational disruptions and reputational damage, MFA is an essential security measure. It’s also mandated for the regulated Brazilian iGaming market, where operators must submit proof of compliance.

In this blog, Luana Monje, Brazil-based Sales Executive at Continent 8 Technologies, explores the significance of MFA in Brazil’s exciting market, highlighting its role as both a regulatory cybersecurity requirement, outlining key considerations when selecting an effective authentication platform, and showcasing Continent 8’s passwordless MFA solution designed to deliver the most seamless single-step PIN experience.
According to the Secretariat of Prizes and Bets (SPA) and the Ministry of Finance’s (MF) technical and cybersecurity guidelines for Brazil’s betting systems (Ordinance No. 722, available in Portuguese), MFA is defined as:
A type of authentication that uses two or more of the following elements to verify a user’s identity: information known only to the user, such as a password, a pattern, or answers to challenge questions; an item owned by a user, such as an electronic token, a physical token, or an identification card; a user’s biometric data, such as fingerprints, facial or voice recognition.
First and foremost, Brazilian regulations require the implementation of MFA across several technical and cybersecurity requirements outlined in Ordinance No. 722. These requirements include:
Ordinance 722, Annex I, sections 12, 13 and 16 – Access to the betting system:
a) at least once every 7 (seven) days; or
b) on the first access after a period of inactivity of more than 7 (seven) days.
Ordinance 722, Annex IV, section 25f – Technical Controls, DNS requirements:
25 – The following requirements apply to servers used to resolve Domain Name System (DNS) queries in association with the betting system:
f) multi-factor authentication must be in place
MFA provides a layer of cybersecurity that significantly mitigates the risk of unauthorised access, thereby safeguarding sensitive data and personal information.
With MFA being a regulatory requirement in Brazil, iGaming and online sports betting operators need to evaluate which MFA options are most suitable for their operations. Here are some key considerations when assessing an MFA platform, and how Continent 8 can support your MFA journey.
| Key Consideration | The Continent 8 MFA Advantage |
|---|---|
| User experience | Same passwordless, 2-second, single-step login – on all devices and browsers
99.9% of users log in within 2 seconds. Supports biometric auth in apps. Our MFA solution ensures consistent user experiences across both app and browser platforms, while also offering the option of local biometric authentication for apps. |
| Compatibility / Operability | 100% of devices, 100% of browsersOur MFA solution ensures complete independence from hardware or operating systems, enabling compatibility across all devices and platforms.
By providing our solution through the same browser interface as the operator’s service, or by embedding the technology directly into the operator’s native app, we support:
|
| Login success rate | 99.93% login success or higherOur MFA platform streamlines the login process to a passwordless, single user step. The system is capable of operating with either a PIN or biometric authentication, providing users with flexibility and a reliable fallback across any device or browser.
Each additional step increases the potential for user error, and every dependency (such as downloads, installations, mobile phones, cellular networks, or username entry) introduces a potential point of failure for both users and the system. Our platform achieves a 99.93% login success rate in consumer-facing applications, using either a 4-digit PIN or device-based biometric authentication where available. Our platform also attains a 99.997% success rate in action (transaction) authentication. There is no difference in success rates between mobile and tablet/laptop devices, as the system does not rely on the presence of a mobile device. |
| Registration success rate | +18% in player registrations, 20% boost in profitsOur MFA solution’s enrolment process simply requires users to select a 4-digit PIN. This procedure does not require any permissions, downloads, plug-ins, imported keys or configurations, thereby eliminating registration failures. The enrolment can be completely invisible and take place during customer registration.
User process – on any device or browser:
The result: +18% increase in user registrations which can boost profits by up to 20%. |
| Support costs | 90% savings in support costs
Our MFA solution minimises support-related expenses and resources with a self-sufficient service. For example, this platform eliminates the need for password reset assistance – accounting for up to 60% of support desk inquiries, costing an estimated $15-70 per call – and customer validation. |
| MSSP services | 360-degree support
As an MSSP, we offer comprehensive end-to-end support for seamless evaluation, deployment, and ongoing assistance by:
|
| Technology | Minimal attack surface, no single point of failure
Our MFA solution employs advanced zero-knowledge proof of identity, ensuring a minimal trust surface and eliminating any single point of failure. Provides robust two-factor authentication, with the option of a software-only solution. |
| Data privacy | Zero information required
Our MFA solution does not require any Personally Identifiable Information (PII) from the end user. Instead, we only need a unique identifier, which may be a hash of a mobile number, email address, or username, thereby ensuring the solution’s adaptability to various identity schemes. |
The iGaming and online betting industry is constantly evolving, with new technologies and threats emerging regularly. Multi-factor authentication is an essential component of future-proofing betting and gaming platforms against these evolving risks. By integrating advanced authentication methods, iGaming and online sports betting operators can stay ahead of cyber threats and continuously protect their systems and players’ data.
Continent 8 is committed to supporting businesses in the iGaming and online sports betting industry with their cybersecurity needs. Our team of experts works closely with you to design and implement tailored MFA solutions that align with your regulatory requirements and business objectives.
To learn more about Continent 8’s MFA solution, contact Luana at luana.monje@continent8.com.
Jerad Swimmer, Regional Sales Director at Continent 8 Technologies, explores the benefits of a cybersecurity checklist to safeguard your tribal gaming operations against emerging cyber threats and attacks.

Safeguarding your business can be daunting, and you might be asking yourself ‘where do I begin?’ To address this, we have prepared a cybersecurity checklist to help you identify possible weaknesses.
First, let us set the scene with the current state of play and why you need to prioritize cybersecurity in today’s world.
The tribal gaming industry is a vibrant and vital part of many Native American communities, providing not only entertainment but also significant economic benefits. However, this industry is increasingly falling under the crosshairs of sophisticated cybercriminals. These bad actors aim to disrupt operations, steal sensitive patron data and extort ransom payments. The stakes are high, with the potential impact extending beyond the casino floors to tribal governments, health services and community trust.
Cyber threats in tribal gaming are diverse and evolving. For example, ransomware attacks have become more prevalent, demonstrating a devastating capacity to bring operations to a standstill. A recent notable incident involved a ransomware attack that compromised all internet servers and data, with the attackers demanding up to $500,000 to restore services. These incidents highlight the urgent need for comprehensive cybersecurity measures tailored to the unique environment of tribal casinos.
The consequences of a cyber attack on a tribal casino can be far-reaching. Beyond the immediate financial losses and operational disruptions, there is a profound impact on the trust and confidence of the community. Patrons expect their personal and financial information to be secure, and any breach can lead to a significant erosion of trust.
To effectively combat cyber threats, tribal casinos need to adopt a multi-faceted cybersecurity strategy. This involves not just technological solutions but also organizational practices and policies. The foundation of such a strategy includes:
Continent 8, supported by our dedicated cybersecurity company, C8 Secure, is a trusted partner for tribal nations and gaming enterprises. Our cybersecurity services are tailored to meet the unique needs of tribal governments, regulators and casino operators.
Our capabilities include:
We are trusted by a diverse array of tribal gaming casinos and organizations, including ShowNation, Tachi Palace Casino Resort, among others.
Don’t wait for an incident to discover whether you’re vulnerable. By taking these proactive steps, tribal casinos can fortify their defenses, ensuring uninterrupted operations and maintaining the trust of their communities.
Secure your tribal gaming operations by accessing this detailed checklist.
Continent 8 provides comprehensive, multi-layered threat prevention, detection and response solutions to secure your tribal organization’s digital assets in the face of evolving cyber threats. For more information on how Continent 8 can support your cybersecurity initiatives, email sales@continent.com or fill out our Contact Us page.