

Blueprint Gaming is a leading UK-based game studio and part of Germany’s Gauselmann Group. The company develops innovative slot games for the global online and mobile markets, with titles also available across more than 100,000 land-based gaming terminals in the UK, Germany, and Italy.
Blueprint Gaming had been using an incumbent SIEM tool that offered technology but not the expertise and operational support of a fully managed SOC.
As a lean infrastructure team operating in a high-risk, data-intensive industry, Blueprint needed:
Without additional specialist resources, maintaining a proactive security posture was becoming increasingly challenging.
Blueprint selected Continent 8’s Managed Security Operations Centre (MSOC) — a complete, fully managed security service integrating an advanced SIEM platform operated by Continent 8’s cybersecurity specialists.
Key capabilities delivered included:
This combination of technology, people, and process provided the 24/7 monitoring and threat response Blueprint required – without increasing internal workload.
Continent 8 delivered a robust managed security solution combining a leading technology stack with expert cybersecurity professionals who operate and manage the environment on Blueprint’s behalf.
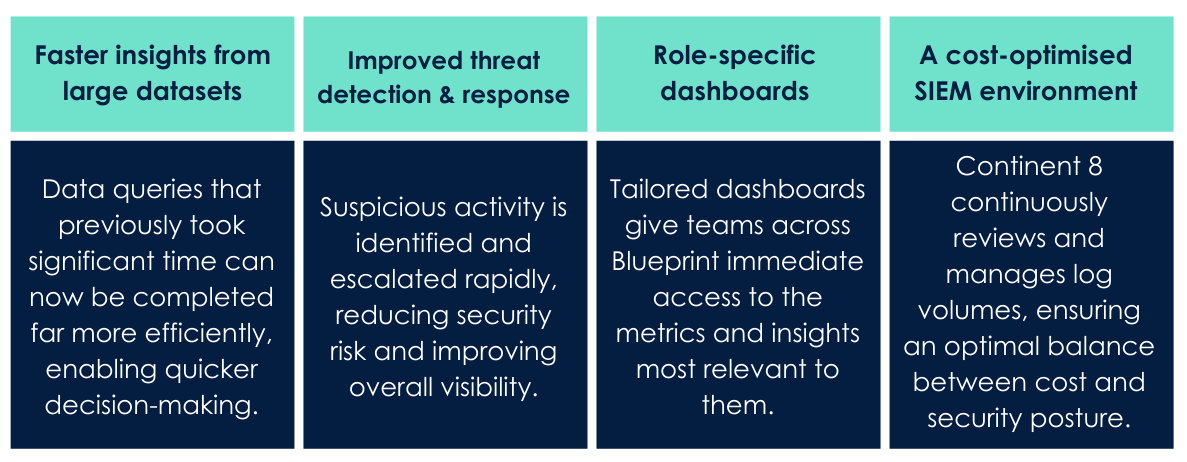
Outcomes included:
Adam Shepherd, Head of Infrastructure at Blueprint
“We’re a small team that manages huge volumes of data in a high-risk industry. Managing that effectively – without compromising security – was a real challenge for us. That’s where Continent 8 stepped in, providing a managed SOC service with a strong focus on the threat landscape. They’ve enabled quicker responses to threats and equipped us with simplified dashboards. Working with the team has been a real pleasure.”
Patrick Gardner, Chief Security Officer at Continent 8
“Blueprint required strong security oversight without adding operational burden to a lean internal team. Our Managed SOC service was designed to deliver exactly that – improving visibility, accelerating threat detection, and optimising log volumes while maintaining a robust security posture. The result is a scalable, cost-efficient security capability aligned to the realities of a high-risk, data-intensive environment.”
Click to download the PDF version