Cybersecurity regulation in Europe is evolving rapidly, and iGaming businesses must prepare now for two major incoming frameworks: the NIS2 Directive and the EU cyber resilience act (CRA). These regulations introduce stricter security obligations, tighter reporting deadlines and heightened accountability across the iGaming ecosystem.

In our recent webinar, “iGaming’s new cybersecurity rules”, Oliver Crofton (Regional Sales Director – Cybersecurity at Continent 8 Technologies) hosted an in‑depth discussion with Craig Lusher (Principal Solutions Architect EMEA at Continent 8 Technologies) and Jo Joyce (Partner and Head of Regulatory, IP & Digital at Taylor Wessing Ireland). Together, they provided clarity on the regulatory landscape and outlined what operators, suppliers and technology partners must do to stay ahead.
Here’s a breakdown of the key takeaways.
WHY NIS2 AND THE CRA MATTER FOR IGAMING
The iGaming industry operates in a high‑risk digital environment. Real-time financial transactions, complex technology stacks, and large volumes of sensitive personal data (including government-issued identity documents attached to financial information) make it a prime target for attackers. As cyber threats grow more sophisticated, regulators are raising the bar to ensure resilience.
NIS2 and the CRA aim to:
- Improve cybersecurity across critical and digital sectors
- Strengthen supply‑chain security
- Hold organisations – and their senior leadership – accountable to higher, consistent standards
- Ensure digital products and platforms are secure throughout their lifecycle
For iGaming, where uptime, trust and compliance underpin commercial success, these changes are significant.
NIS2: BROADER SCOPE AND HIGHER STANDARDS
NIS2 is fully live and enforcement has begun. This is no longer about preparation; the question is whether your organisation is compliant right now.
According to Craig and Jo, NIS2 represents a major overhaul of Europe’s cybersecurity framework. It replaces the original NIS Directive (2016), which was fragmented, voluntary in practice, and allowed each country to implement it differently.
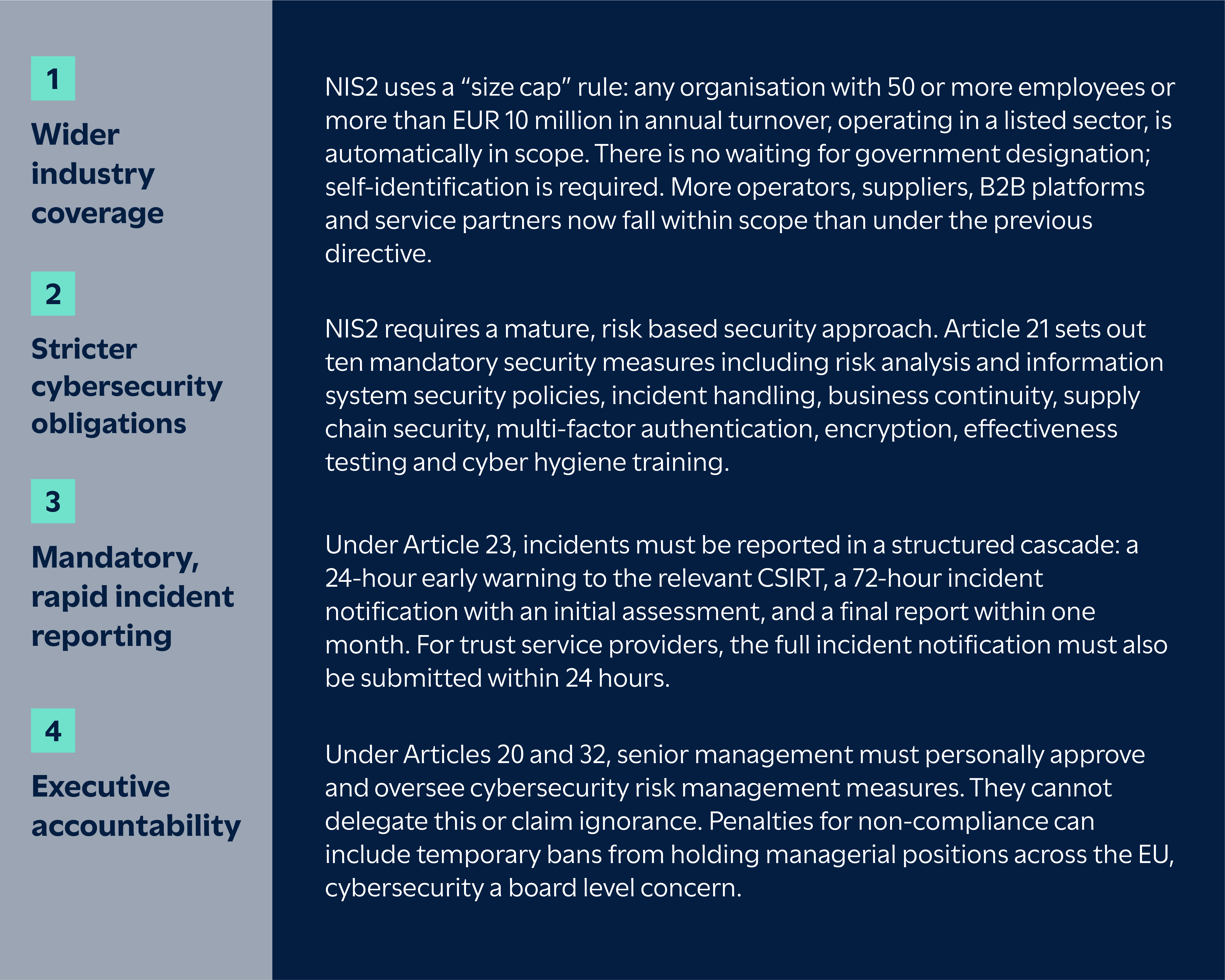
Key updates include:
THE EU CYBER RESILIENCE ACT: SECURITY BY DESIGN
Whilst NIS2 focuses on how organisations manage security, the CRA concentrates on the digital products those organisations depend on and produce.
CRA reporting obligations begin on 11 September 2026. From that date, manufacturers must report actively exploited vulnerabilities and severe incidents affecting the security of their products, following the same 24-hour early warning, 72-hour notification structure. For vulnerabilities, the final report must be submitted within 14 days of a corrective measure becoming available. Full product standards, including CE-marking requirements for software and connected devices, come into force in December 2027.

Jo highlighted that the CRA requires manufacturers and developers of digital tools – including gaming software, APIs, hardware and integrated systems – to
- Build security into products from day one
- Maintain an active vulnerability‑management process
- Deliver timely patches and updates
- Guarantee security throughout the entire product lifecycle, with a minimum support period of five years
Given the heavy reliance on third‑party tech in iGaming, this places strong emphasis on vendor due diligence and supply‑chain oversight.
ARE YOU IN SCOPE? MOST LIKELY.
Jo: “I think one of the things that I’ve spotted is quite a lot of operators and firms within the iGaming ecosystem haven’t really necessarily accepted that they’re in scope.”
If your organisation provides or supports any of the following, NIS2 likely applies:
- Gaming platforms or remote gaming servers
- Hosting, cloud or infrastructure services
- Game content or content delivery
- Payment solutions (these may also fall under DORA)
- Managed services or operational support
- Identity or authentication services
There are two additional points worth flagging. First, white-label and B2B providers are often managed service providers (MSPs) without realising it. If you run a player account management (PAM) system for 20 other brands, you are managing their core services, which, by definition, makes you an MSP. Under NIS2, MSPs are designated as essential entities, meaning they face ex ante supervision (proactive inspections and audits at any time), the same regulatory tier as a data centre or cloud provider.
Second, there is no “group privilege” under NIS2. If an internal IT arm provides services to the wider corporate group, it may be classified independently as an essential entity in its own right. Being part of a larger group does not shield individual subsidiaries or divisions from independent classification.
A readiness assessment is the essential first step.
THE THREAT LANDSCAPE: GROWING IN COMPLEXITY
Craig emphasised how the threat landscape facing iGaming businesses has intensified – including a 400% surge in cyber attacks targeting the gambling industry. This is not a gradual trend; attackers have industrialised their approach.

Operators and suppliers now face:
- AI‑powered attack techniques (such as deepfakes targeting video KYC processes)
- A significant increase in credential‑stuffing and account takeover attempts
- Ransomware and extortion campaigns
- Exploits originating from third‑party integrations (supply chain)
- Attacks targeting uptime and availability during peak sporting events
The interconnected nature of the sector amplifies the impact of any single vulnerability.
The cost of downtime in the industry now exceeds $6,000 per minute, and attacks are more visible in the news than ever, and recent breaches have seen hundreds of thousands of user profiles and identity documents exposed through relatively basic misconfigurations.
ARE ALL EU COUNTRIES FOLLOWING THE SAME RULES?
Craig highlighted several country‑specific differences in how NIS2 is being implemented, here are a few examples:
Malta
Malta moved faster than most EU member states, issuing Legal Notice 71 of 2025, with the CIPD as the ‘competent authority’. Self‑registration was due September 2025, so organisations that missed the deadline are now operating in a regulatory grey area. Governance and risk‑management controls must be live by March 2026, which at the time of the webinar was just weeks away.
Malta also goes further than EU baseline requirements by mandating a 24/7 security operations centre for digital infrastructure providers. Properly staffing a round-the-clock SOC requires at least 12 people to maintain a true rotation, which is a substantial operational investment for mid-sized operators.
The ultimate sanction isn’t just a fine; Malta can suspended MGA licences. For Malta-licensed gaming companies, this is an existential threat. If you lose your MGA licence, you are effectively locked out of dozens of global markets overnight.
Germany
Germany passed its implementation late, in November 2025. Registration deadlines for German‑based entities land in April 2026, leaving limited time for compliance.
Other member states are at various stages of transposition, and several missed the original October 2024 deadline. For operators with a presence in multiple EU countries, the practical challenge is managing compliance against several different national timelines and requirements simultaneously.
IMPLEMENTATION IN OTHER EU MEMBER STATES
NIS2 is an EU directive, which means each member state must transpose it into national law. The result is that implementation timelines and specific requirements vary from country to country, and organisations operating across multiple jurisdictions need to track each one independently.
LEADERSHIP MUST BE ACTIVELY INVOLVED
Both speakers stressed that NIS2 and the CRA require visible, ongoing engagement from senior management. Leading organisations will:
- Make cybersecurity a regular board agenda item
- Establish direct communication between security leads and executives
- Invest in long‑term cybersecurity maturity
- Build a culture where every department understands its responsibilities
Under NIS2, leadership accountability is explicit. Executive training is not optional; it is a legal requirement under the directive.
Jo: “Just because something bad has happened doesn’t mean that you’re necessarily at fault… but you are going to have to produce reasonable reporting in layman’s terms… and explain that we’re operating in different risk parameters.”
Craig added the importance of training: “It’s mandatory for board‑level staff… you’ve got to keep training and constant training.”
REPORTING REQUIREMENTS
Craig and Jo discussed the importance of reporting – especially when something goes wrong.
Jo: “The kind of reporting that one has to do under NIS2 is not a million miles away from the pre‑existing reporting… but there’s a real shift when you are experiencing a very serious incident.”
The 24‑hour reporting window is the operational flashpoint. Many companies are not ready for this. Under NIS2, the clock starts as soon as you become aware of a significant incident. You then have 24 hours to submit an early warning to the relevant CSIRT, 72 hours for a more detailed incident notification, and one month for the final report. A single incident can also trigger reporting obligations under the CRA and DORA simultaneously, each with different data requirements, formats, timelines and regulators.
Businesses need to prepare now by having supplier lists to hand, knowing exactly where to submit reports for each applicable regulation, and understanding that multi-jurisdictional reporting may be required.
Top tip from Jo:
Please print out a copy of your breach response plan… print out your incident response team list with phone numbers, ideally personal ones. If you can’t access your systems, it will take you an astonishing amount of time to pull this together.
ENFORCEMENT: WHAT BUSINESSES SHOULD EXPECT
Jo highlighted that enforcement activity under the CRA and NIS2 will be phased but increasingly serious.
From September 2026, the CRA introduces mandatory reporting of actively exploited vulnerabilities and severe incidents affecting product security. Full product‑related obligations take effect in December 2027, including the requirement for CE‑marking digital products, software included.
According to Jo, failure to report will likely be the first area where regulators take action, and penalties will be treated seriously.
Many NIS2 requirements are already enforceable. For essential entities that breach Articles 21 or 23, fines can reach up to EUR 10 million or 2% of total worldwide annual turnover, whichever is higher. For important entities, the maximum is EUR 7 million or 1.4% of worldwide turnover (Article 34 of NIS2). Regulators also have the power to issue binding instructions, order security audits, and, for essential entities, temporarily suspend or prohibit individuals from exercising managerial functions (Article 32(5)).
Jo: “They will factor in whether it’s going to bankrupt you… but they want these fines to hurt.”
This means businesses must act now to ensure reporting pathways, governance structures, supplier oversight and security controls are ready.
HOW TO PREPARE: PRACTICAL STEPS HIGHLIGHTED IN THE WEBINAR
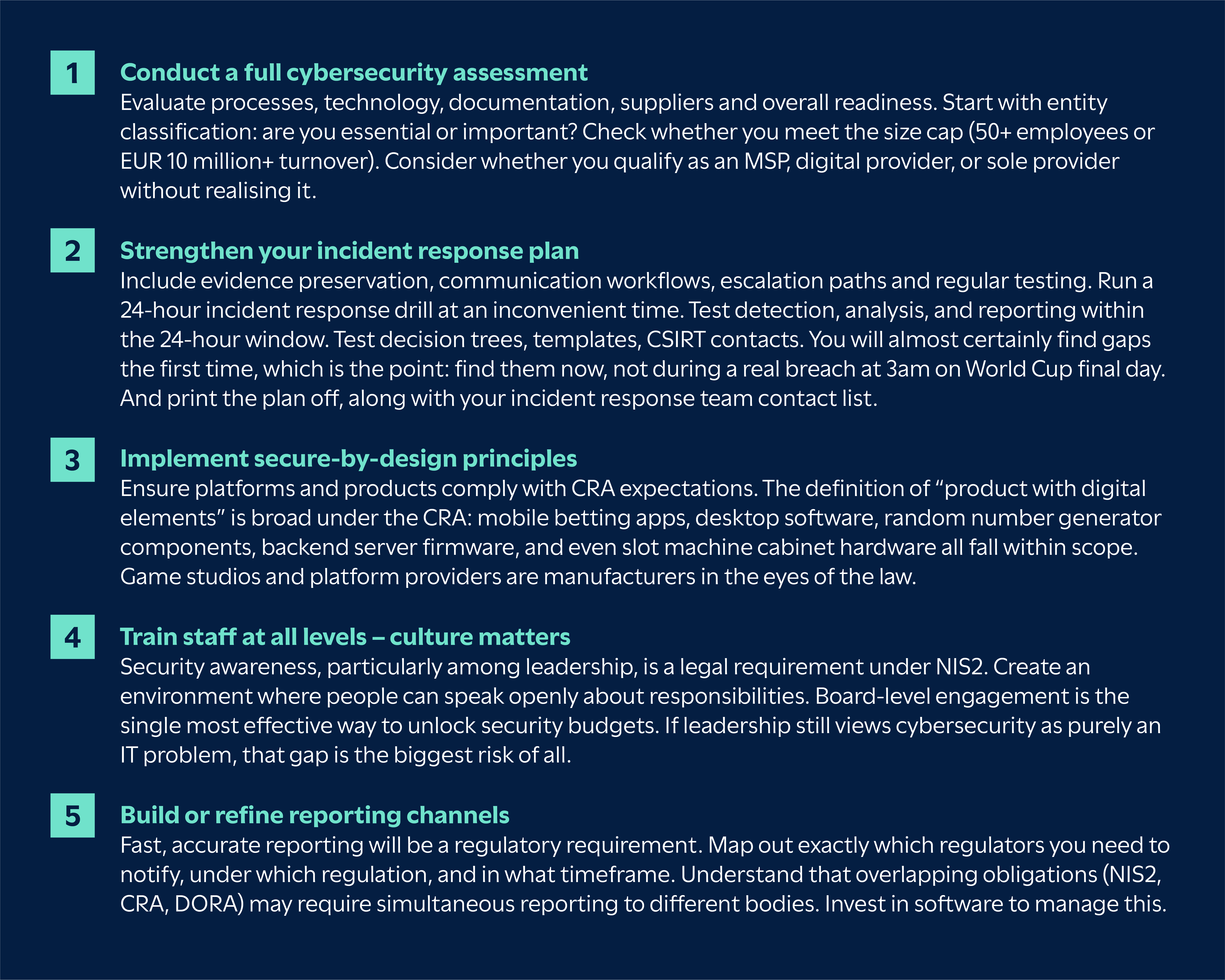
Craig and Jo recommended several clear actions for organisations:
ADDRESS OPEN-SOURCE SOFTWARE OBLIGATIONS
There is a growing issue around the use of open‑source software (OSS) under the CRA. Although many OSS developers lobbied for exemption, OSS is widely used in commercial products. The CRA makes clear that organisations relying on OSS within regulated products remain fully responsible for meeting all cybersecurity and update obligations, including providing security updates for the minimum five-year support period.
Managing updates is difficult when you did not write the code – but the responsibility remains. The Software Bill of Materials (SBOM) requirement compounds this: manufacturers must maintain a machine-readable inventory of every library, open-source component and module in their products, kept as a living record.
Top tip from Jo:
If your business relies heavily on OSS, pay close attention to how it’s managed, seek specialist guidance and plan how you will meet long‑term update and security requirements.
FINAL THOUGHTS
The introduction of NIS2 and the EU cyber resilience act marks a significant shift for cybersecurity in iGaming. While the regulations bring real compliance challenges, they also create an opportunity for the industry to strengthen its defences, reduce operational risk and future‑proof operations.
Early preparation will help businesses stay compliant, competitive and trusted.
👉 Watch the full webinar here: